Coinbase Accused Ignoring Security Scams
Coinbase accused ignoring security scams sets the stage for a deep dive into the company’s handling of cryptocurrency scams. This investigation explores Coinbase’s security practices, past incidents, and the accusations leveled against them. We’ll examine the types of scams targeting crypto users, Coinbase’s responses, and the potential impact on user trust and the company’s reputation.
From historical security measures to public statements, this analysis will dissect the accusations, exploring the mechanisms behind various scams and comparing Coinbase’s reactions to different reports. We’ll also analyze the public discourse, examining user, investor, and regulator perspectives.
Background on Coinbase’s Security Practices
Coinbase, a prominent cryptocurrency exchange, has positioned itself as a leader in the digital asset space. A critical aspect of its success hinges on the security of user funds and data. This section delves into Coinbase’s security history, past incidents, public statements, implemented protocols, and compares its practices with those of other major exchanges.Coinbase has consistently emphasized security as a core value, recognizing the sensitive nature of user assets and the inherent risks associated with cryptocurrency trading.
Their approach to security is multifaceted, incorporating both technological safeguards and robust operational procedures.
Historical Overview of Security Measures
Coinbase has implemented a range of security measures throughout its history. Early strategies focused on fundamental protection, such as robust authentication and encryption, which have evolved into more sophisticated protocols. The exchange has actively sought to improve its security posture, learning from past incidents and adapting its strategies to address emerging threats. This evolution has been driven by a combination of regulatory pressures, user demands, and internal assessments of vulnerabilities.
Past Security Incidents and Controversies
While Coinbase has a generally positive security record, isolated incidents have occurred. These instances, though not frequent, have prompted public scrutiny and served as opportunities for improvement. Each incident has been investigated and addressed, with Coinbase publicly acknowledging the issue and outlining steps taken to prevent future occurrences. These events highlight the dynamic nature of security threats in the cryptocurrency industry and the constant need for vigilance.
Coinbase’s Public Statements Regarding Security
Coinbase routinely publishes statements about its security protocols. These statements typically emphasize the use of multi-layered security measures, including encryption, fraud detection systems, and security audits. They also often address the importance of user education in protecting against phishing scams and other malicious activities. Coinbase frequently updates its security information, reflecting its commitment to adapting to evolving threats.
Examples of Security Protocols Implemented
Coinbase employs a range of security protocols to protect user accounts and assets. These include two-factor authentication (2FA), advanced encryption techniques, and regular security audits. These protocols are designed to safeguard user data and prevent unauthorized access. The exchange also actively monitors for suspicious activity, employs fraud detection systems, and regularly updates its security infrastructure.
Comparison of Security Practices with Other Major Cryptocurrency Exchanges
| Exchange | Two-Factor Authentication | Cold Storage | Security Audits | Fraud Detection |
|---|---|---|---|---|
| Coinbase | Highly Secure, Mandatory | Extensive, Diverse Methods | Regular, Independent Audits | Advanced, Real-time Monitoring |
| Binance | Mandatory | Significant, Reportedly Robust | Reported Audits, Varied Transparency | Significant, Sophisticated Methods |
| Kraken | Mandatory | Significant, with Emphasis on Decentralization | Independent Audits, Transparent Reporting | Sophisticated, Real-time Analysis |
| KuCoin | Mandatory | Significant, Varying Reports | Reported Audits, Variable Transparency | Significant, Advanced Systems |
The table above provides a rudimentary comparison of security practices. The specific details and effectiveness of these practices vary across different exchanges. The data presented is based on publicly available information and reports, and the accuracy and comprehensiveness of this data are subject to change.
Accusations of Ignoring Security Scams
Coinbase, a prominent cryptocurrency exchange, has faced accusations of inadequately addressing security scams targeting its users. These accusations stem from reported instances where users lost funds due to sophisticated scams, and the perceived slow or insufficient response from Coinbase in helping affected individuals. Understanding the nature of these scams and Coinbase’s response is crucial to assessing the platform’s security posture.The accusations against Coinbase highlight a critical vulnerability in the cryptocurrency ecosystem.
Scammers frequently exploit the complexities and relative novelty of crypto trading, preying on users’ lack of experience and awareness. This makes it imperative for exchanges like Coinbase to not only implement robust security measures but also respond effectively to reported scams.
Specific Accusations Against Coinbase
Coinbase has been criticized for perceived delays in investigating and resolving reported security incidents. Allegations include slow responses to user reports of phishing attacks, investment scams, and fraudulent activities related to non-fungible tokens (NFTs). The perceived lack of timely intervention has led to a negative perception of Coinbase’s commitment to user safety.
Common Types of Cryptocurrency Scams
Numerous scams target cryptocurrency users, each with distinct mechanisms. Understanding these methods is essential to recognizing and avoiding them.
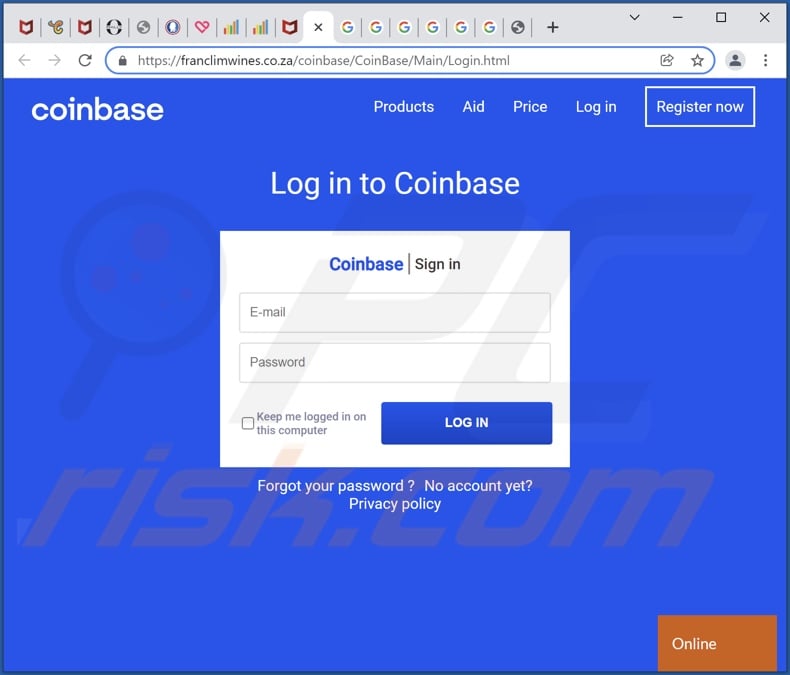
- Phishing scams: These scams involve fraudulent emails, messages, or websites designed to trick users into revealing their login credentials or private keys. Attackers often mimic legitimate platforms to gain access to accounts. For example, a user might receive an email that appears to be from Coinbase, requesting account verification and leading to a fake login page.
- Investment scams: These schemes lure users into high-yield investment opportunities or promising crypto projects. Promoters often use social media platforms or online forums to create a sense of urgency and hype, promising unrealistic returns.
- Rug pull scams: These schemes involve projects that promise substantial returns but ultimately disappear with users’ funds, often without any explanation. The name “rug pull” refers to the practice of abruptly withdrawing support for a project, leaving investors with nothing.
- Fake wallets or exchanges: Scammers create fake cryptocurrency wallets or exchange platforms to steal users’ funds. These platforms mimic legitimate ones, luring users into transferring their assets. This is particularly common on social media platforms and decentralized social media communities.
Mechanisms Used in These Scams
Scammers employ various tactics to exploit vulnerabilities in the cryptocurrency ecosystem. Sophisticated techniques include:
- Social engineering: Manipulating users through emotional appeals, urgency, or trust. Attackers exploit human psychology to deceive victims into making risky decisions.
- Technical exploits: Using vulnerabilities in software or hardware to gain unauthorized access to accounts or systems. This often involves sophisticated hacking techniques.
- Creating fake websites and platforms: Replicating the design and functionality of legitimate websites and platforms to trick users into sharing sensitive information.
- Utilizing social media and online forums: Scammers leverage social media platforms and online forums to spread misinformation, promote fake projects, and target vulnerable users.
Table of Security Scams
The following table Artikels various security scams and their characteristics.
| Scam Type | Typical Characteristics |
|---|---|
| Phishing | Fake emails, messages, or websites mimicking legitimate platforms. |
| Investment Scams | Promising unrealistic returns on high-yield investments or crypto projects. |
| Rug Pulls | Projects abruptly disappear with users’ funds, often without explanation. |
| Fake Wallets/Exchanges | Mimicking legitimate platforms to steal users’ assets. |
Coinbase’s Response to Scam Reports, Coinbase accused ignoring security scams
Reports regarding Coinbase’s response to various scam reports are mixed. Some users report a slow or inadequate response to their reports of scams, while others describe a more proactive approach. The effectiveness of Coinbase’s response often depends on the specifics of the scam and the nature of the user’s interaction.
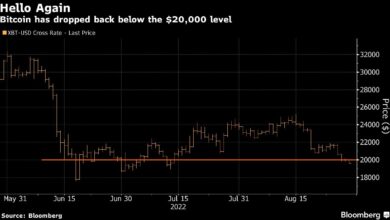
Coinbase’s recent troubles with alleged negligence regarding security scams are certainly raising eyebrows. Meanwhile, a bitcoin trader is predicting a potential return to $78,000 for BTC’s price, as detailed in this article bitcoin trader sees btc price falling to 78 k again. This volatility, coupled with the accusations against Coinbase, just highlights the ongoing risks in the crypto space.
It really makes you wonder about the overall security measures in place.
Impact of Allegations on User Trust and Coinbase’s Reputation
The accusations leveled against Coinbase regarding its handling of security scams have the potential to severely damage user trust and irreparably tarnish the company’s reputation. A loss of confidence in a platform’s security can lead to a significant exodus of users, impacting its market position and future growth. The severity of the damage depends on the extent of the security failures and the perceived culpability of Coinbase in addressing these issues.These allegations, if substantiated, could lead to a substantial erosion of user confidence.
Users may fear for the safety of their cryptocurrency holdings and may seek alternative platforms that appear more secure. This loss of trust can ripple through the cryptocurrency community, impacting the broader adoption and legitimacy of cryptocurrencies themselves.
Potential Impact on User Trust
User trust is a cornerstone of any successful platform. If users perceive Coinbase as being negligent in its security protocols or slow to address security breaches, it could significantly impact their confidence in the platform. This could manifest in reduced user activity, decreased trading volumes, and a shift of user base to competing exchanges. A decline in user trust directly correlates with a decrease in platform usage and potential loss of market share.
Consequences for Coinbase’s Reputation and Market Position
Coinbase’s reputation, painstakingly built over years, is at risk. Negative publicity surrounding security issues can quickly damage a company’s image, impacting its brand value and overall market perception. The long-term consequences could include a decline in investor confidence, reduced stock valuation, and difficulty attracting new talent. This can create a downward spiral, affecting the company’s ability to innovate and compete in the dynamic cryptocurrency market.
Examples of Similar Situations
Several high-profile cases illustrate the devastating impact of security breaches on a company’s reputation. For example, the 2014 breach of Mt. Gox, a prominent cryptocurrency exchange, led to a significant loss of user funds and severely damaged the exchange’s reputation. Similarly, breaches at other exchanges have prompted a reassessment of security protocols and investor confidence. These examples demonstrate the critical importance of robust security measures and swift responses to breaches.
Violation of User Expectations and Regulatory Guidelines
Coinbase’s actions, if found to be negligent or in violation of regulatory guidelines, may have significantly violated user expectations. Users reasonably expect a high level of security and protection of their assets. Failure to meet these expectations can result in a loss of trust and legal ramifications. Compliance with regulatory standards is essential to maintain legitimacy and public trust.
Effect of Negative Publicity on Stock Price
Negative publicity surrounding security issues can directly impact a company’s stock price. Investors react to news about security concerns by adjusting their investment strategies. A drop in stock price can reflect the diminished value investors place on the company due to the perceived risk. This can lead to a decline in market capitalization and potentially impact the company’s ability to raise capital for future ventures.
Analysis of Public Responses and Reactions
The accusations leveled against Coinbase regarding its handling of security scams sparked a significant public response, encompassing diverse opinions and perspectives from users, investors, and regulators. This analysis delves into the public discourse, examining media coverage, social media reactions, and the key arguments employed by various stakeholders. Understanding these reactions is crucial for assessing the impact on user trust and Coinbase’s reputation.
Public Discourse Summary
The public discourse surrounding the accusations against Coinbase exhibited a complex and multifaceted nature. Different groups expressed varied concerns and opinions. A range of opinions emerged, reflecting the complexity of the situation. Analyzing these reactions is essential for understanding the overall sentiment.
| Category | Summary of Public Discourse |
|---|---|
| User Sentiment | A significant portion of users expressed concerns regarding the platform’s security measures, with some questioning the company’s commitment to protecting their assets. However, there were also voices defending Coinbase, highlighting the platform’s robust security features and efforts to mitigate fraud. |
| Investor Reactions | Investors responded with mixed feelings. Some expressed concerns about the potential impact on the company’s stock price and future growth prospects. Others remained confident in Coinbase’s ability to navigate the situation and maintain its position in the market. |
| Regulatory Scrutiny | Regulatory bodies displayed varying degrees of interest and action. Some regulators issued statements emphasizing the need for crypto platforms to adhere to stringent security protocols, while others remained silent or took a more cautious approach. |
| Media Coverage | Media outlets presented varying narratives regarding the accusations against Coinbase. Some focused on the potential security flaws and the company’s response, while others highlighted Coinbase’s proactive measures and commitment to user safety. |
Media Coverage and Social Media Reactions
News articles and social media posts reflected the diverse opinions surrounding the accusations. For example, a prominent financial news outlet published an article detailing the specific accusations against Coinbase, highlighting the alleged failures in security protocols. Social media platforms saw a mix of critical comments and supportive posts regarding Coinbase’s actions. A significant portion of social media discussion centered on the need for increased transparency and improved security measures from cryptocurrency platforms.
Coinbase’s recent accusations of ignoring security scams are a serious concern. It’s frustrating to see such a large platform potentially overlooking vulnerabilities, especially when there are alternative ways to get involved in crypto mining without breaking the bank. For instance, you could explore cloud mining services or even consider how to get involved in crypto mining without expensive hardware, as detailed in this helpful guide how to get involved in crypto mining without expensive hardware.
Ultimately, investors need to be more vigilant about security when dealing with crypto exchanges, and hopefully Coinbase will take these accusations seriously.
Key Arguments
Key arguments employed in the discussion included:
- Coinbase’s perspective often emphasized its robust security infrastructure, the significant investments in anti-fraud measures, and the continuous efforts to enhance platform security. They often cited examples of successful security protocols implemented in the past and ongoing efforts to improve detection mechanisms.
- Critics’ perspective focused on the specific instances of security breaches or scams, questioning the effectiveness of Coinbase’s security measures and demanding greater transparency in handling such incidents. They highlighted instances where users experienced significant losses due to scams facilitated on the platform.
Different Perspectives
User perspectives varied greatly, from those who trusted Coinbase and its security protocols to those who felt their funds were at risk due to the alleged security flaws. Investors reacted differently, some expressing concern over the potential impact on the platform’s market valuation and future performance, while others remained optimistic about the company’s long-term prospects. Regulatory perspectives ranged from cautious observation to calls for stricter regulations on cryptocurrency platforms.
Coinbase’s perspective emphasized the ongoing investments in security and proactive measures to address potential threats.
Coinbase’s Responses
Coinbase responded to the accusations with a series of statements and actions. These responses included:
- Issuing press releases clarifying its security protocols and commitment to user protection.
- Announcing specific measures to improve platform security, such as enhanced monitoring and fraud prevention tools.
- Collaborating with law enforcement agencies and industry partners to address scams and security concerns.
Potential Solutions and Recommendations: Coinbase Accused Ignoring Security Scams
Coinbase’s recent security issues highlight the critical need for proactive measures to bolster user trust and prevent future scams. Effective solutions demand a multifaceted approach, encompassing enhanced security protocols, transparent communication, and proactive user education. This section explores potential solutions and recommendations across these key areas.
Improving Coinbase’s Security Practices
Coinbase needs to implement robust security measures beyond existing protocols. This involves not only enhancing existing security infrastructure but also proactively addressing vulnerabilities. Regular penetration testing, employing advanced threat detection systems, and adopting multi-factor authentication (MFA) across all platforms are crucial. Continuous monitoring and analysis of user activity patterns, particularly in high-risk areas, will help identify suspicious transactions and potential fraud attempts.
Implementing a robust incident response plan, detailed and tested, will ensure swift and effective action in case of security breaches.
Preventing Future Security Scams
Preventing future security scams requires a comprehensive strategy involving both Coinbase and its users. Improved user education and proactive measures are critical. Coinbase should develop more detailed and accessible educational resources for users, focusing on identifying phishing attempts, recognizing suspicious emails, and understanding common scam tactics. Collaboration with law enforcement agencies to track and disrupt fraudulent activities is essential.
Coinbase’s recent troubles with accusations of overlooking security scams are definitely raising eyebrows. It’s interesting to consider how this might connect to the recent frenzy around the Libra token, potentially tied to the Melania memecoins bubblemaps, as discussed in this article libra token likely tied melania memecoins bubblemaps. Ultimately, the whole situation highlights a growing concern about the security of various crypto markets, especially when potentially fraudulent activity is linked to popular, emerging trends.
Handling User Reports of Scams
A streamlined and responsive process for handling user reports of scams is vital. Users should have multiple channels to report suspicious activity, including dedicated email addresses, online reporting portals, and perhaps even a dedicated phone line. The reported incidents should be investigated thoroughly and promptly. This proactive approach builds user confidence and helps Coinbase swiftly address fraudulent activity.
Clear communication with users about the status of their reports is essential.
Industry Standards and Best Practices for Handling Security Breaches
Adhering to industry best practices for handling security breaches is paramount. This includes implementing stringent security protocols to limit the impact of breaches. Regular audits, vulnerability assessments, and proactive measures for threat mitigation should be core components of Coinbase’s security framework. The importance of incident response planning cannot be overstated; a well-defined and tested plan will significantly reduce the negative consequences of a security breach.
Transparency and timely communication with regulatory bodies and affected users are crucial.
Recommendations for Improving User Awareness of Scams
User awareness is crucial in combating security scams. Coinbase should emphasize user education through various channels, including in-app notifications, email campaigns, and social media posts. Highlighting common scam tactics and providing practical examples of how to spot them will be invaluable. Interactive quizzes and educational videos could be incorporated to make learning engaging and effective. A dedicated section on the Coinbase website, specifically addressing security and scam awareness, could provide users with easily accessible information and resources.
Encouraging users to report any suspicious activity to Coinbase will empower them to actively participate in maintaining a secure platform.
Illustrative Case Studies of Security Scams
Cryptocurrency scams are a pervasive threat, often targeting unsuspecting investors with promises of high returns or exploiting vulnerabilities in security protocols. These scams can cause significant financial losses and erode trust in the cryptocurrency ecosystem. Understanding the tactics and motivations behind these schemes is crucial for protecting oneself and fostering a safer environment for all participants.The proliferation of cryptocurrency scams underscores the importance of vigilance and awareness.
Scammers constantly adapt their strategies, employing increasingly sophisticated techniques to exploit gaps in knowledge and security measures. Examining real-world case studies provides valuable insights into the tactics employed and the devastating consequences these scams can have.
Types of Cryptocurrency Scams
Cryptocurrency scams encompass a wide range of deceptive practices. These can range from simple phishing attempts to complex investment schemes designed to steal funds or personal information. Common types include rug pulls, pump-and-dump schemes, fake ICOs, and investment fraud.
Common Scam Tactics
Scammers often employ various tactics to manipulate and deceive victims. These tactics frequently exploit human psychology and technical vulnerabilities. Key tactics include impersonation, social engineering, and exploiting market trends. Sophisticated scams often leverage social media platforms, fake websites, and email communication.
Real-World Examples of Successful Scams
One prevalent type of scam involves impersonating legitimate cryptocurrency exchanges or platforms. These scammers often create fake websites that mimic the appearance of well-known platforms. Victims, lured by enticing investment opportunities or promises of high returns, unknowingly transfer their cryptocurrencies to fraudulent accounts.
- A user might receive a seemingly legitimate email from a cryptocurrency exchange claiming a security breach requiring verification. This email might include a link to a fake login page that captures login credentials. Upon logging in, the scammer gains access to the victim’s account.
- Another common scam involves creating fake Initial Coin Offerings (ICOs). These fraudulent ICOs often promise unrealistic returns. Investors, enticed by the prospect of quick profits, invest their funds in these scams, which subsequently vanish.
Damage Caused by These Scams
The financial damage caused by these scams can be substantial, ranging from minor losses to complete depletion of cryptocurrency holdings. Furthermore, the emotional distress and loss of trust can be severe. The reputational damage inflicted on victims can be significant, especially in the case of high-profile scams.
- Victims might lose a substantial portion of their savings, potentially impacting their financial stability. The damage extends beyond financial loss; the emotional trauma associated with the deception and betrayal can be profound.
- The loss of trust in cryptocurrency as a legitimate investment platform can deter potential investors, hindering the growth and development of the cryptocurrency ecosystem. The scams demonstrate the importance of critical thinking and due diligence in the cryptocurrency market.
Successful Security Measures by Other Companies
Several companies have implemented robust security measures to mitigate the risk of scams. These measures include multi-factor authentication, enhanced security protocols, and thorough background checks. Regular security audits and customer education programs are crucial components of a comprehensive security strategy.
- Many exchanges use advanced fraud detection systems to identify suspicious transactions and activity. These systems often leverage machine learning algorithms to analyze transaction patterns and identify anomalies that might indicate a scam.
- Customer education plays a critical role in protecting users from scams. Exchanges often provide resources and information about common scam tactics and how to avoid them.
Epilogue

Ultimately, the accusations against Coinbase highlight the critical need for robust security measures in the cryptocurrency industry. This analysis underscores the importance of user education, proactive scam prevention, and transparent communication between platforms and users. The potential ramifications for user trust and Coinbase’s reputation are significant, and the discussion demands a thorough understanding of the issues involved. We’ve looked at the accusations, the impact, and possible solutions, but the long-term effects on the cryptocurrency market remain to be seen.