Phantom Wallet Phishing Fake Update Attack
Phantom wallet users targeted fake update phishing attack highlights a sophisticated cyberattack targeting users of a specific digital wallet. This attack leverages the vulnerabilities in user awareness and the potential for social engineering to achieve its goals. The attack likely involves a deceptive fake update, tricking users into downloading malicious software. This article will explore the various facets of this attack, from its technical execution to the potential impact on users and platforms.
This detailed exploration will cover the methods employed by attackers, the potential consequences for victims, and preventative measures. The discussion will also delve into user behavior and security best practices to mitigate the risks of falling prey to such attacks.
Defining the Attack Vector
Phantom wallets, a seemingly innocuous concept, are a crucial element in understanding the sophisticated tactics employed in phishing attacks. These are essentially digital wallets that don’t exist. They are a fictional construct used by cybercriminals to lure unsuspecting users into providing sensitive information or installing malicious software. The attackers prey on the users’ desire to access or manage their cryptocurrencies.Understanding phantom wallets and the associated attack vectors is critical to recognizing and preventing these scams.
Criminals often use social engineering techniques, creating a sense of urgency or legitimacy to trick victims into actions that compromise their accounts or systems.
Phantom Wallet Definition
A phantom wallet is a fabricated digital wallet that doesn’t correspond to any legitimate cryptocurrency account. It’s designed to mimic a real wallet, often appearing authentic to the untrained eye. These wallets are not controlled by legitimate cryptocurrency platforms or exchanges and are solely under the control of the attackers. This deceptive nature is central to the effectiveness of the attacks.
Methods for Identifying Phantom Wallet Users
Identifying potential victims is a key part of a phishing campaign. Attackers utilize various methods to target individuals who might be more susceptible to these scams. They may employ social media data, publicly available information, or even purchase lists of users who have interacted with cryptocurrency platforms in the past. Sophisticated methods also use machine learning to analyze user behavior and predict potential targets.
Characteristics of a “Fake Update” Phishing Attack, Phantom wallet users targeted fake update phishing attack
A fake update phishing attack leverages the perceived need for users to update their wallets or accounts. This approach capitalizes on the fear of missing out (FOMO) and the natural desire to keep systems up-to-date. Critically, the fraudulent update often contains malicious code or redirects the user to a malicious website, thereby compromising their account or device. The fake update typically uses a deceptive email or message that mimics legitimate communication from the targeted cryptocurrency platform.
The fake update also frequently includes a sense of urgency or a limited-time offer to further manipulate the user.
Phantom wallet users recently fell victim to a sneaky fake update phishing attack. It’s a real bummer, and unfortunately, these scams are becoming more common. Thankfully, there are some exciting developments in the crypto world, like Velora becoming Para Swap, which is a promising step forward. Velora is now Para Swap, introduces a new set of features, hopefully, making things safer for users in the future.
This is a good reminder to always double-check any updates before clicking and downloading. It’s important to remain vigilant against these types of attacks.
Stages of a Phishing Attack Targeting Phantom Wallet Users
Phishing attacks targeting phantom wallet users generally follow a predictable sequence of steps. These steps are designed to create a sense of legitimacy and urgency to manipulate users into providing sensitive information.
- Preparation and Reconnaissance: Attackers meticulously research their targets, gathering information on their potential victims and their preferred cryptocurrency platform. This information allows them to tailor their phishing attempts to specific individuals, thereby increasing the chance of success.
- Delivery of the Bait: The attackers craft a convincing email or message that appears to come from a legitimate source. This message often includes urgent requests or false claims to manipulate the target into taking action. For example, it might falsely claim that the wallet requires an update to prevent security breaches.
- Luring the User into the Trap: The crafted message usually directs the target to a fake website that mimics the actual platform’s login page. The user is encouraged to enter their credentials, believing they are interacting with a trusted platform.
- Exploitation and Data Extraction: Upon entering their details, the user unknowingly provides the attackers with sensitive information such as usernames, passwords, and private keys, thus compromising their account and any associated cryptocurrencies.
- Exit Strategy: The attackers then use the stolen credentials or data to gain access to the target’s cryptocurrencies or other valuable information.
Types of Phishing Techniques
The following table Artikels various phishing techniques, emphasizing their different approaches to deception. Each technique uses specific tactics to target users.
| Phishing Technique | Description | Example |
|---|---|---|
| Deceptive Phishing | This is the most common type of phishing attack, characterized by impersonating a legitimate entity to trick the user into revealing sensitive information. | An email claiming to be from a bank asking for account details. |
| Spear Phishing | This technique targets specific individuals or organizations by using personalized information gathered from various sources to increase the likelihood of success. | A targeted email to a specific employee within a company, referencing their recent purchase history. |
| Whaling | A more sophisticated type of spear phishing that targets high-profile individuals or executives, often using detailed information to manipulate them into revealing sensitive data. | An email addressed to a CEO, requesting urgent action on a critical financial matter. |
| Pharming | This attack redirects users to a fraudulent website that mimics a legitimate one. The user unknowingly enters their credentials on the fake site. | A user is redirected to a fake banking website while attempting to access their online banking portal. |
Impact and Consequences
Phantom wallet attacks, while seemingly a niche issue, carry significant repercussions for users, platforms, and the broader financial ecosystem. The consequences extend beyond mere financial loss, encompassing reputational damage and legal complexities. Understanding these potential impacts is crucial for both users and developers to proactively mitigate risks.The potential financial losses for targeted users can be substantial, ranging from minor inconveniences to complete loss of funds.
A successful attack can lead to the theft of cryptocurrency holdings, and the loss of associated value, potentially impacting users’ financial stability. The severity of the impact is directly proportional to the amount of cryptocurrency held in the compromised wallet.
Financial Losses for Targeted Users
The financial impact of a successful phantom wallet attack on individual users can vary widely. The most obvious consequence is the direct loss of cryptocurrency. This loss can be significant, particularly for users holding substantial amounts of digital assets. Beyond the direct financial loss, users may also face additional costs related to recovering their accounts or assets.
Furthermore, users may experience a loss of trust in the platform, potentially impacting their future engagement with the platform or the wider cryptocurrency ecosystem.
Reputational Damage for Affected Platforms
A phantom wallet attack can severely damage the reputation of a cryptocurrency platform. Loss of user trust is a significant concern. Negative publicity can deter potential users and investors, leading to a decline in platform value and market share. A successful attack highlights security vulnerabilities and a lack of robust security protocols. Such attacks can erode the confidence of the public and the broader financial community.
A lack of swift and transparent responses to the attacks can further exacerbate the reputational damage.
Legal Ramifications for Those Involved in the Attack
Legal ramifications for those involved in a phantom wallet attack can be severe. Depending on the jurisdiction, individuals or groups responsible for such attacks can face criminal charges, including theft, fraud, and potentially conspiracy. The legal process can be complex and protracted, potentially involving international cooperation. The specific legal consequences depend on the jurisdiction, the nature of the attack, and the amount of cryptocurrency stolen.
Comparison of Phantom Wallet Attacks to Other Financial Fraud
Phantom wallet attacks share similarities with other types of financial fraud, but they also present unique challenges. Like traditional fraud schemes, phantom wallet attacks exploit vulnerabilities and manipulate users. However, the decentralized nature of cryptocurrency and the anonymity of some transactions can make investigation and prosecution more complex. The rapid evolution of the cryptocurrency landscape and the emergence of new attack vectors contribute to the complexity.
Methods for Recovery from Such Attacks
Recovery from a phantom wallet attack is a complex process with no guaranteed outcome. The most important step is to report the attack to the platform and relevant authorities immediately. This allows for investigations and potentially the recovery of assets. Utilizing cybersecurity experts and legal professionals is often crucial for effective recovery. However, the likelihood of recovering all stolen assets depends on various factors, including the swiftness of the response and the specifics of the attack.
Often, recovery may not be complete, and the attack leaves lasting consequences for the victim.
Motivations and Tactics
Phantom Wallet users targeted by fake update phishing attacks face a calculated threat. Attackers aren’t simply seeking to cause annoyance; their motivations are driven by financial gain and often involve sophisticated strategies. Understanding these motivations and tactics is crucial for individuals to protect themselves from falling victim to these schemes.
Likely Motivations
Attackers are driven by the desire to steal sensitive information, such as login credentials, financial data, and personal information. The motivations often extend beyond simple theft to encompass the potential for financial gain through illicit activities, such as selling stolen data on the dark web or engaging in further fraudulent schemes. This underscores the need for robust security measures to deter and counteract such malicious activities.
Attack Strategies
Attackers employ a range of strategies to exploit vulnerabilities and entice victims. These tactics often leverage psychological manipulation, creating a sense of urgency or fear to prompt immediate action. These strategies are meticulously planned to target specific user groups, understanding their potential vulnerabilities and behaviors. The attackers use a combination of social engineering and technical exploits to increase the success rate of their attacks.
Role of Social Engineering
Social engineering plays a significant role in these attacks. Attackers leverage psychological manipulation to trick users into downloading malicious software or divulging sensitive information. This includes crafting convincing messages that mimic legitimate updates or notifications, creating a sense of urgency and trust. Attackers may use emotional manipulation, such as fear or curiosity, to pressure victims into responding to their requests.
Technical Vulnerabilities
Attackers often exploit known or unknown technical vulnerabilities in software or systems to gain unauthorized access. These vulnerabilities may be present in the Phantom Wallet software itself or in the operating systems used by the victims. Sophisticated attackers may employ zero-day exploits, taking advantage of previously unknown weaknesses. Such vulnerabilities can be leveraged to install malicious software, gain unauthorized access, or disable security measures.
Distribution Methods of Fake Updates
Fake updates are distributed through various channels, including email, text messages, social media, and malicious websites. Attackers often disguise the malicious content to appear legitimate, such as using official-looking logos and branding. Phishing emails often mimic legitimate communication, while fake websites can look identical to the genuine website, creating an environment of trust and deception. This requires users to exercise extreme caution when interacting with suspicious emails, messages, or websites.
For example, checking the sender’s email address for inconsistencies, verifying the authenticity of the website, and using multi-factor authentication (MFA) are crucial steps in mitigating this threat.
- Email Phishing: Attackers send emails that appear to be from a legitimate source, such as Phantom Wallet. These emails often contain links to malicious websites or attachments containing malware.
- Malicious Websites: Attackers create fake websites that mimic the legitimate Phantom Wallet website. These websites are designed to collect user credentials or install malware.
- Social Media: Attackers may use social media platforms to distribute fake update information, aiming to entice users to visit malicious websites or download malicious software.
User Behavior and Awareness: Phantom Wallet Users Targeted Fake Update Phishing Attack
Falling prey to phishing attacks often boils down to predictable human behaviors. Understanding these patterns is crucial for developing effective defense strategies. Users need to be aware of the tactics employed by malicious actors and the common vulnerabilities they exploit. This knowledge empowers them to make informed decisions and safeguard their digital assets.
Common Behaviors Leading to Vulnerability
Users often exhibit certain behaviors that make them susceptible to phishing attacks. These behaviors include a tendency to trust apparent legitimacy, a lack of skepticism about unsolicited communications, and a failure to recognize subtle inconsistencies in messages. A lack of awareness regarding the importance of strong security practices and the recognition of phishing attempts can significantly increase the risk of compromise.
Impatience and a desire for immediate gratification also play a role. Users may rush through the verification process or click on links without thoroughly checking their legitimacy.
Strategies for Improving User Awareness
Effective user awareness training plays a vital role in mitigating the impact of phishing attacks. Training programs should cover various aspects of phishing techniques, such as recognizing suspicious email subject lines, identifying common red flags, and understanding the importance of strong security practices. Simulations of phishing attacks can provide valuable insights into user behavior and reinforce the importance of vigilance.
Educating users about the potential consequences of falling victim to phishing attacks can motivate them to take necessary precautions.
Phantom wallet users recently fell victim to a fake update phishing attack, highlighting the ever-present threat of scams in the digital space. Thankfully, companies like Blofin are proactively improving user experience and security by expanding their unified trading accounts. This focus on platform efficiency with blofin powers up platform efficiency with unified trading account expansion is a smart move to bolster security against precisely these types of attacks.
It’s important for users to stay vigilant and aware of these threats, even as companies work hard to provide better protection.
Best Practices for Avoiding Phishing Attacks
Users can significantly reduce their vulnerability by adhering to established best practices. These best practices are Artikeld in the table below:
| Best Practice | Description |
|---|---|
| Verify Sender Identity | Always carefully review the sender’s email address and domain. Look for inconsistencies or misspellings that may indicate a fraudulent attempt. |
| Be Suspicious of Urgent Requests | Do not feel pressured to act immediately. Phishing emails often create a sense of urgency to trick users into making hasty decisions. |
| Never Click on Suspicious Links | Avoid clicking on links within emails from unknown senders. Instead, navigate to the official website directly. |
| Report Suspicious Emails | Flag or report suspicious emails to the appropriate authorities or your email provider. |
| Update Software Regularly | Keep your software, including operating systems and applications, updated to patch security vulnerabilities. |
| Use Strong Passwords | Employ strong, unique passwords for all online accounts to prevent unauthorized access. |
Examples of Common Phishing Email Subject Lines
Phishing emails frequently employ subject lines designed to create a sense of urgency, curiosity, or importance. Examples include:
- Urgent Account Action Required
- Important Security Update
- Suspicious Activity Detected on Your Account
- Verification Needed for Your Phantom Wallet
- Congratulations! You’ve Won a Prize
Importance of Strong Security Practices
Strong security practices are essential for protecting against phishing attacks. Robust security measures, such as strong passwords, multi-factor authentication, and regular software updates, can significantly reduce the risk of falling victim to malicious attacks. Implementing these practices creates a multi-layered defense system, making it harder for attackers to compromise accounts and sensitive information. Furthermore, maintaining a strong security posture can help preserve the reputation of the organization and protect its clients from potential financial and reputational damage.
“A strong security posture is not just a technical requirement, but a fundamental aspect of responsible digital citizenship.”
Technical Analysis of the Attack

Phantom Wallet users targeted by a fake update phishing attack faced a sophisticated delivery method designed to exploit user vulnerabilities. This involved a meticulous plan to trick victims into downloading malicious software disguised as legitimate updates. Understanding the technical nuances of this attack is crucial for both prevention and detection.The attack leveraged common user behavior, particularly the tendency to update software without thoroughly scrutinizing the source.
This reliance on automatic update mechanisms or the perceived need for software upgrades created a critical vulnerability. Attackers capitalized on this by creating convincing simulations of official updates, leading unsuspecting users to unknowingly download malicious files.
Fake Update Delivery Mechanisms
This attack often utilizes various delivery methods. These can include: malicious links embedded in emails, messages, or social media posts. These links may appear legitimate but redirect to compromised websites hosting the malicious software. The attackers may also use fake update installers disguised as legitimate software, often leveraging social engineering to gain user trust. Moreover, infected websites or compromised software repositories might serve as delivery points.
This vector often leverages vulnerabilities in existing software or web applications.
Exploited Vulnerabilities
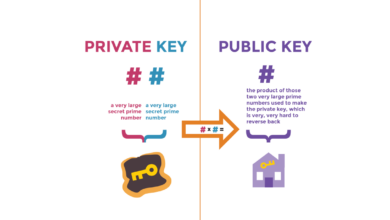
The primary vulnerability exploited is the trust users place in software updates. This attack leverages the psychological aspects of perceived legitimacy and urgency. Attackers capitalize on user’s reliance on software updates, bypassing crucial security protocols by creating convincing facades. The attack may also leverage software vulnerabilities (if present) in the target applications. By exploiting this trust, attackers can bypass security measures and gain access to user devices.
Technical Prevention Measures
Preventing these attacks requires a multi-layered approach: Implement robust security measures to monitor and control software updates. Users should be educated on verifying update sources. Employing strong authentication mechanisms on all platforms, such as two-factor authentication, can significantly reduce the impact of phishing attacks. Keeping operating systems and applications updated with the latest security patches is essential to mitigate known vulnerabilities.
Employing intrusion detection systems can alert to suspicious activity. Finally, regular security audits and vulnerability assessments are critical for identifying and patching potential weaknesses in the system.
Automated Detection Potential
Automated detection of these types of attacks is possible through various techniques. Security information and event management (SIEM) systems can analyze network traffic for suspicious patterns, such as downloads of known malicious files. Machine learning algorithms can identify anomalies in user behavior, flagging potential phishing attempts. By monitoring downloads, file activities, and user behavior, security tools can effectively detect suspicious patterns associated with the attack.
Attack Vectors and Technical Characteristics
| Attack Vector | Technical Characteristics |
|---|---|
| Malicious Email Links | Phishing emails containing links that redirect to malicious websites. The links may mimic legitimate update links, using spoofed addresses or domain names. |
| Fake Installers | Malicious software disguised as legitimate software updates. These installers might contain embedded malware or exploit vulnerabilities in the target system. |
| Compromised Websites | Compromised websites that serve malicious files masquerading as legitimate software updates. This can involve injecting malicious code into web pages or exploiting vulnerabilities in web applications. |
| Infected Software Repositories | Compromised software repositories that distribute malicious software updates. This often involves attackers manipulating the software distribution channels to replace legitimate updates with malicious ones. |
Security Measures and Prevention

Protecting your digital wallet from phishing attacks requires a multi-layered approach, focusing on both user awareness and robust technical safeguards. This section details critical security protocols and best practices to mitigate the risk of falling victim to fraudulent updates and other similar attacks. Wallet platforms need to prioritize proactive security measures to ensure user trust and financial safety.
Robust Security Protocols
Implementing strong security protocols is paramount for preventing phishing attacks. These protocols act as a layered defense, making it significantly harder for malicious actors to exploit vulnerabilities. Strong passwords, combined with multi-factor authentication, provide a critical first line of defense. Regular software updates patch known vulnerabilities, hindering attackers’ ability to exploit weaknesses.
- Strong Passwords: Use unique and complex passwords for each account, avoiding easily guessable phrases or personal information. Employ a password manager to securely store and generate strong passwords, and avoid reusing passwords across different platforms.
- Multi-Factor Authentication (MFA): Implement MFA wherever possible. This adds an extra layer of security, requiring users to verify their identity using multiple methods beyond a simple password. This could include a one-time code sent to a phone, a security key, or biometric authentication.
- Regular Software Updates: Keeping software up-to-date is crucial. Patches often address vulnerabilities that malicious actors might exploit. Automated update systems minimize user effort while maximizing security.
- Security Awareness Training: Educate users about phishing tactics and red flags to identify suspicious emails, messages, or websites. Regular training reinforces best practices and encourages vigilance.
Securing Wallet Platforms
Wallet platforms must prioritize security from the ground up. This includes implementing robust security measures at every stage of the user journey, from registration to transaction processing.
- Secure Communication Channels: Utilize encrypted communication channels (HTTPS) for all user interactions. This prevents attackers from intercepting sensitive data during transmission.
- Regular Security Audits: Conduct periodic security audits to identify and address potential vulnerabilities in the platform’s code and architecture. This proactive approach ensures the platform remains secure against evolving threats.
- Data Encryption: Encrypt sensitive data both in transit and at rest. This protects data even if unauthorized access occurs.
- Whitelisting: Implement a whitelisting system for known and trusted applications or websites. This limits access to only authorized sources, preventing malicious applications from interacting with the platform.
Multi-Factor Authentication (MFA) Implementation
MFA significantly enhances security by requiring multiple verification steps beyond a password.
- Choosing an MFA Method: Select an MFA method that aligns with the platform’s user base and technical capabilities. Common methods include one-time codes sent via SMS, authenticator apps, and security keys.
- User Interface Design: Clearly guide users through the MFA process, providing clear instructions and error messages. Make the process as seamless and user-friendly as possible to encourage adoption.
- Security Key Integration: Integrate support for security keys where possible. Security keys provide a hardware-based authentication method that is extremely resistant to phishing and other attacks.
Importance of Regular Software Updates
Software updates are not just a convenience; they are a necessity for maintaining security. Vulnerabilities are constantly discovered and exploited, and updates often contain critical patches to address these weaknesses.
Speaking of security risks, it’s a bummer that phantom wallet users fell victim to a fake update phishing attack. Meanwhile, innovative companies like catizen are partnering with Google Cloud to develop AI virtual pets, reshaping the global pet industry ecosystem here. It’s a stark reminder that even with these advancements, vigilance against scams like these phishing attempts remains crucial for protecting our digital assets.
- Vulnerability Management: Establish a process for identifying and addressing software vulnerabilities. Regular security scans and vulnerability assessments help identify potential weaknesses before they can be exploited.
- Automated Updates: Implement automated update systems where feasible. This ensures that users receive security patches without requiring manual intervention, thereby reducing the risk of delay and potential exploitation.
- Testing and Validation: Thoroughly test updates in a controlled environment before deploying them to production. This helps identify any unforeseen issues and ensures a smooth transition.
Security Best Practices for Wallet Platforms
A comprehensive approach to security requires a combination of technical and operational strategies.
| Security Best Practice | Description |
|---|---|
| Strong Passwords | Require strong, unique passwords for all accounts. |
| Multi-Factor Authentication (MFA) | Implement MFA to add an extra layer of security. |
| Regular Software Updates | Keep software up-to-date with security patches. |
| Security Awareness Training | Educate users about phishing and security threats. |
| Secure Communication Channels | Use encrypted communication channels (HTTPS). |
| Regular Security Audits | Conduct periodic security audits to identify vulnerabilities. |
| Data Encryption | Encrypt sensitive data in transit and at rest. |
| Whitelisting | Limit access to only trusted applications or websites. |
Case Studies and Real-World Examples
Unfortunately, detailed, publicly available case studies of specific phantom wallet phishing attacks are rare. This lack of transparency makes it difficult to comprehensively analyze past incidents and draw definitive conclusions about attack methodologies and victim responses. However, we can glean insights from broader trends in cryptocurrency scams and phishing attacks to understand potential scenarios and strategies employed by attackers.
Analysis of Common Attack Methodologies
The methods employed in phantom wallet phishing attacks often mirror broader phishing techniques. Attackers frequently leverage social engineering tactics, creating a sense of urgency or exclusivity to entice victims to download malicious software or disclose sensitive information. This might involve posing as legitimate wallet support teams or promising substantial rewards. In some cases, the attack might involve exploiting vulnerabilities in existing software, making it seem like a genuine wallet update.
These vulnerabilities could allow attackers to gain access to user accounts and funds. The common thread across these attacks is the exploitation of human psychology and the creation of a deceptive environment.
Examples of Victim Responses
Victims of phantom wallet attacks often fall into predictable response patterns. Many victims may panic and attempt to quickly resolve the issue, leading them to follow the attacker’s instructions more readily. This is a common human response in situations where urgency is implied. Others may be more cautious and attempt to verify the legitimacy of the update or request through official channels.
Variations in individual reactions depend on factors such as technical knowledge, experience with cryptocurrency, and the level of deception employed by the attackers. Critically, the speed and complexity of the attacker’s actions can influence the victim’s response.
Effectiveness of Existing Security Measures
The effectiveness of existing security measures in preventing phantom wallet attacks is often limited by the inherent complexity of the attacks themselves. Traditional security measures, such as firewalls and antivirus software, may not always detect or block the specific type of malicious software used in these attacks. A significant challenge is the rapid evolution of attack techniques, meaning that security measures often lag behind.
User awareness and education play a crucial role in mitigating the impact of these attacks. Furthermore, the lack of centralized reporting and data sharing makes it difficult to identify emerging trends and patterns in these attacks, which hampers the development of effective countermeasures. This means that preventative measures need to be multifaceted, addressing both technical vulnerabilities and user behavior.
Summary Table of Key Takeaways
| Case Study Feature | Description |
|---|---|
| Attack Methodology | Typically involves social engineering, impersonation, and exploitation of vulnerabilities. |
| Victim Response | Often characterized by panic and a desire to quickly resolve the issue, leading to increased susceptibility to fraudulent requests. |
| Effectiveness of Security Measures | Limited by the rapid evolution of attack techniques and the need for enhanced user education and awareness. |
Future Trends and Predictions
The landscape of online threats is constantly evolving, and phishing attacks targeting cryptocurrency wallets, like Phantom, are no exception. Understanding emerging trends and anticipating potential future threats is crucial for maintaining security. Adapting to these evolving techniques is paramount to effectively safeguarding user assets.
Emerging Trends in Phishing Attacks
Phishing attacks are becoming increasingly sophisticated, leveraging social engineering tactics to exploit user vulnerabilities. The rise of AI-powered tools is enabling attackers to personalize phishing campaigns with greater accuracy, making them more difficult to detect. Furthermore, the integration of legitimate-looking web services with malicious payloads, often targeting specific user groups, is a growing concern. Attackers are also becoming more adept at using legitimate domains and infrastructure to host their malicious content, making it harder for security systems to identify suspicious activity.
Potential Future Threats to Wallet Security
One potential future threat is the use of advanced machine learning algorithms to create highly realistic fake websites and emails. These attacks would be significantly more difficult to detect, requiring more sophisticated security measures. Another concern is the exploitation of emerging technologies, such as the metaverse, for phishing attacks. As more users engage with these virtual worlds, new attack vectors will likely emerge.
A further concern is the rise of “spear-phishing” attacks that are tailored to specific individuals or groups. These attacks exploit detailed personal information gathered from social media and other online sources, increasing the effectiveness of the attack.
Evolution of Attack Strategies
Attack strategies are continuously adapting to evade existing security measures. This includes the use of increasingly sophisticated techniques to bypass email filters and security protocols. A key observation is the integration of social media and other online platforms into the phishing process. Attackers are using these platforms to spread misinformation and lure victims into clicking malicious links.
Moreover, there’s a growing trend of using compromised legitimate accounts to spread phishing campaigns, making it harder for users to distinguish between legitimate and malicious communications.
Need for Ongoing Security Research
Security research plays a vital role in staying ahead of evolving attack techniques. Researchers need to constantly analyze emerging threats and develop new detection methods. This includes investigating the use of AI in phishing attacks and developing new countermeasures. Furthermore, researchers should focus on understanding the psychological factors that contribute to phishing susceptibility. This allows for the creation of more effective user awareness programs.
Importance of Continuous Adaptation to Evolving Attack Techniques
Continuous adaptation to evolving attack techniques is critical. Security measures need to be regularly updated to address new threats and vulnerabilities. Furthermore, continuous improvement in user awareness programs is essential. This involves educating users about the latest attack methods and strategies. Finally, collaboration between security researchers, wallet developers, and users is crucial in mitigating the impact of phishing attacks.
Conclusion
In conclusion, phantom wallet users targeted fake update phishing attack underscores the ever-evolving nature of cyber threats. The attackers’ use of fake updates demonstrates a creative approach to exploiting user trust. Protecting yourself requires a multifaceted approach, combining robust security measures with a keen awareness of potential threats and a proactive approach to security. This discussion has covered the complexities of the attack, offering insights for both users and platform administrators.