HTX Ventures Report Stablecoins & RWAs in DeFi
The role of stablecoins and RWAs in DeFi HTX Ventures report sets the stage for understanding the critical role of stablecoins and Reserve-Based Assets (RWAs) in the burgeoning DeFi ecosystem. This report delves into the advantages, risks, and future outlook for these crucial elements in the world of decentralized finance. It examines the different types of stablecoins, their functions, and the security measures employed to mitigate potential vulnerabilities.
The report also explores the impact of RWAs on DeFi protocol stability and security. It analyzes the key findings, trends, and challenges surrounding the adoption and innovation of stablecoins, providing insights into the regulatory landscape affecting their use within DeFi platforms. The report’s analysis is structured to show market trends, challenges, and the future outlook for stablecoins and RWAs in DeFi.
Introduction to Stablecoins and RWAs in DeFi
Stablecoins and Reserve-Based Assets (RWAs) are rapidly emerging as crucial components of the decentralized finance (DeFi) ecosystem. They offer a path towards greater stability and usability within the volatile world of cryptocurrencies. These assets aim to bridge the gap between the traditional financial system and the decentralized realm, enabling a wider range of DeFi applications and functionalities.Stablecoins, designed to maintain a stable value pegged to a fiat currency or other asset, are essential for facilitating transactions and reducing the risks associated with fluctuating cryptocurrency prices.
Reserve-Based Assets, which utilize reserves to maintain their value, offer a robust structure for maintaining stablecoin peg stability. This approach helps to foster trust and encourage wider adoption of DeFi technologies.
Stablecoin Definitions and Types
Stablecoins are cryptocurrencies designed to maintain a stable value, typically pegged to a fiat currency like the US dollar. This stability distinguishes them from other cryptocurrencies, which can fluctuate significantly in value. Their purpose in DeFi is to provide a reliable store of value and a stable medium of exchange, facilitating smoother transactions and reducing the risk of price volatility for users.
Different types of stablecoins employ various mechanisms to achieve this stability.
Types of Stablecoins and Their Functionalities, The role of stablecoins and rwas in defi htx ventures report
- Fiat-collateralized stablecoins: These stablecoins are backed by reserves of fiat currencies, typically held in regulated accounts. Examples include USD Coin (USDC) and Tether (USDT). The stability of these coins hinges on the liquidity and reliability of the backing assets. Their functionality revolves around providing a stable exchange medium for DeFi transactions.
- Crypto-collateralized stablecoins: These stablecoins are backed by a basket of cryptocurrencies. Their value is tied to the combined value of the underlying crypto assets. Maintaining the peg often requires complex algorithms and strategies for managing the cryptocurrency reserves. Their function in DeFi is similar to fiat-collateralized stablecoins, offering a stable exchange medium.
- Algorithmic stablecoins: These stablecoins use algorithms to maintain their peg to a target value. They often employ complex mechanisms that adjust the supply and demand of the coin to maintain stability. This approach can be more volatile than other types, as algorithmic adjustments may not always effectively counteract market forces. However, they can have the potential for lower costs compared to other types.
Reserve-Based Assets (RWAs) in DeFi
Reserve-Based Assets (RWAs) are assets whose value is backed by reserves. In the context of stablecoins, RWAs are the underlying assets that support the stablecoin’s peg to a particular currency. These reserves can comprise fiat currencies, other cryptocurrencies, or a combination of both. The quality and stability of the reserves are crucial for maintaining the stablecoin’s value.
RWAs are a key element in DeFi, providing a stable foundation for transactions and other DeFi applications.
Historical Context of Stablecoins and RWAs
The concept of stablecoins and RWAs has a history rooted in the broader financial world. Early attempts at creating stable currencies date back decades, highlighting the ongoing human need for stable mediums of exchange. The evolution of these concepts in the digital age reflects the increasing sophistication and decentralization of financial systems. The recent surge in DeFi has spurred further innovation in stablecoin design and implementation.
Key Characteristics Differentiating Stablecoins from Other Cryptocurrencies
- Stable Value: The defining characteristic of a stablecoin is its commitment to maintaining a stable value relative to a fiat currency or another asset. This differentiates it from other cryptocurrencies, which are known for their volatility.
- Decentralization: Some stablecoins operate in a decentralized manner, reducing reliance on central authorities and enhancing transparency.
- Liquidity: Stablecoins often have high liquidity, making them readily exchangeable for fiat currencies or other cryptocurrencies.
- Security: A robust reserve backing is often a critical component of maintaining the stability of stablecoins.
Table of Stablecoin Types
| Type | Function | Key Features |
|---|---|---|
| Fiat-collateralized | Stable exchange medium | Backed by fiat reserves; often regulated; generally low volatility. |
| Crypto-collateralized | Stable exchange medium | Backed by crypto reserves; requires complex algorithms for maintaining peg; medium volatility. |
| Algorithmic | Stable exchange medium | Uses algorithms to adjust supply and demand; can have higher volatility; potentially lower costs. |
Stablecoins in DeFi
Stablecoins have become a crucial component of decentralized finance (DeFi) protocols, enabling seamless transactions and facilitating various financial applications. Their pegged value to fiat currencies, like the US dollar, aims to mitigate the volatility inherent in cryptocurrencies, making them attractive for users seeking price stability. However, the very nature of their design introduces inherent risks that DeFi platforms must carefully consider.Stablecoins in DeFi protocols provide a critical bridge between the volatile world of cryptocurrencies and the relative stability of fiat currencies.
They offer a means for users to engage in DeFi activities without the constant risk of substantial price fluctuations. This stability, however, is not absolute and comes with potential vulnerabilities that require careful consideration.
Advantages of Using Stablecoins in DeFi
Stablecoins in DeFi facilitate smoother transactions and reduce the risk of significant losses due to price volatility. They enable the creation of various financial products and services within DeFi, promoting wider adoption and innovation. Liquidity provision, lending, and borrowing become more accessible with stablecoins, as they act as a predictable anchor for these operations.
Potential Risks Associated with Stablecoins and RWAs in DeFi
Stablecoins, while designed for stability, are not immune to risks. The pegged value to fiat currencies can be undermined by factors like large-scale redemptions, regulatory pressures, or issues with the underlying reserves. Similarly, Reserve-backed assets (RWAs) can face risks related to the solvency and management of the reserves. Furthermore, the decentralized nature of DeFi can expose stablecoin systems to hacking and manipulation attempts.
Potential Vulnerabilities and Exploits Targeting Stablecoin Systems
The decentralized nature of DeFi can lead to vulnerabilities that are not present in traditional financial systems. Smart contract vulnerabilities, manipulation of oracle data, and attacks on the underlying reserves are potential threats. Hacking attempts, especially targeting the reserves backing the stablecoin, can have catastrophic consequences. Furthermore, the lack of centralized oversight can exacerbate risks compared to traditional financial institutions.
Comparison of Risks and Rewards of Different Stablecoin Types
The security of different stablecoin types varies significantly. For instance, algorithmic stablecoins rely on complex algorithms that can be disrupted, whereas collateralized stablecoins, such as those backed by reserves of other cryptocurrencies or fiat currencies, are susceptible to issues with the value of their collateral.
| Type | Benefit | Risk |
|---|---|---|
| Algorithmic Stablecoins | Potentially lower costs and higher flexibility | Vulnerability to algorithmic failures, susceptible to manipulation, and often dependent on external factors |
| Collateralized Stablecoins | Generally considered more stable, as they are backed by assets | Risk of collateral devaluation, and vulnerability to issues with the underlying assets |
| Fiat-backed Stablecoins | Usually more stable, as they are backed by fiat currencies | Risk of regulatory changes or restrictions, dependence on the stability of the fiat currency |
Security Measures Implemented by DeFi Platforms to Mitigate Risks
DeFi platforms employ various security measures to mitigate the risks associated with stablecoins. These include rigorous audits of smart contracts, diverse and diversified reserves, and mechanisms to monitor and manage redemption requests. Furthermore, the use of advanced cryptographic techniques and robust security protocols is crucial in protecting stablecoin systems.
RWAs and their Impact on DeFi
Real-world assets (RWAs) are increasingly becoming a crucial component of decentralized finance (DeFi) protocols. Their integration offers the potential to enhance security, stability, and accessibility within the DeFi ecosystem, but also presents unique challenges. This exploration delves into the specifics of RWAs in DeFi, examining their implementation, impact, and limitations.
Examples of RWAs in DeFi Projects
RWAs, encompassing various tangible assets, are finding applications in DeFi projects. These include, but are not limited to, commodities, real estate, and even precious metals. The use of RWAs in DeFi protocols allows users to access and utilize these assets without the complexities of traditional financial systems. For instance, some platforms are exploring using collateralized loans backed by real-world assets, enabling access to credit for users with physical assets.
How RWAs Enhance DeFi Stability and Security
The incorporation of RWAs into DeFi protocols can potentially enhance stability and security. By utilizing real-world assets as collateral, DeFi protocols can mitigate the risk of counterparty defaults, a significant concern in traditional finance. This diversification of assets also helps to reduce the impact of market fluctuations on the protocol’s overall health. A diversified portfolio of assets can potentially improve the stability and resilience of the protocol.
Challenges in Implementing RWAs in DeFi
Several challenges hinder the widespread adoption of RWAs in DeFi. One major obstacle is the complexity of valuing and verifying real-world assets. Standardization and clear regulatory frameworks are still under development, leading to issues with asset identification, verification, and valuation. This complexity can create significant hurdles for DeFi protocols aiming to incorporate RWAs.
Impact of RWAs on the Overall Stability of DeFi Markets
The introduction of RWAs can potentially increase the overall stability of DeFi markets. Diversifying the asset base can help to reduce the impact of extreme price swings in certain asset classes on the entire ecosystem. However, the effectiveness of this diversification depends on the quality and diversity of the RWAs incorporated. The successful integration of RWAs can potentially enhance the resilience of DeFi markets against unforeseen events.
Comparison of Different RWA Strategies in DeFi
Various strategies exist for integrating RWAs into DeFi. These include collateralized lending, yield farming, and even tokenization of physical assets. Each approach has its own strengths and weaknesses, impacting the security, liquidity, and overall stability of the protocol. The effectiveness of each strategy depends on the specific characteristics of the RWA and the DeFi protocol utilizing it.
Table of RWA Types, Underlying Assets, and Use Cases in DeFi
| RWA Type | Underlying Asset | Use Cases in DeFi |
|---|---|---|
| Real Estate | Residential or commercial properties | Collateralized lending, yield farming, fractional ownership |
| Commodities | Gold, silver, agricultural products | Collateralized lending, hedging against price fluctuations, yield farming |
| Precious Metals | Gold, silver, platinum | Collateralized lending, trading, yield farming |
| Art | Paintings, sculptures, etc. | Collateralized lending, fractional ownership, investment |
| Crypto-backed assets | Stablecoins, other crypto assets | Collateralized lending, tokenization, exchange |
HTX Ventures Report
The HTX Ventures report delves into the evolving landscape of stablecoins and reserve-backed assets (RWAs) within the decentralized finance (DeFi) ecosystem. It provides a comprehensive analysis of the current market trends, challenges, and opportunities for these crucial components of DeFi. The report examines the implications of regulatory developments, offering a forward-looking perspective on the future trajectory of stablecoins and RWAs in DeFi.
Key Findings on Stablecoins and RWAs
The report highlights several key findings regarding stablecoins and RWAs in the DeFi space. These findings cover market trends, challenges, and potential future trajectories, all informed by the current DeFi ecosystem. A crucial element in this analysis is the acknowledgment of the growing importance of regulatory compliance.
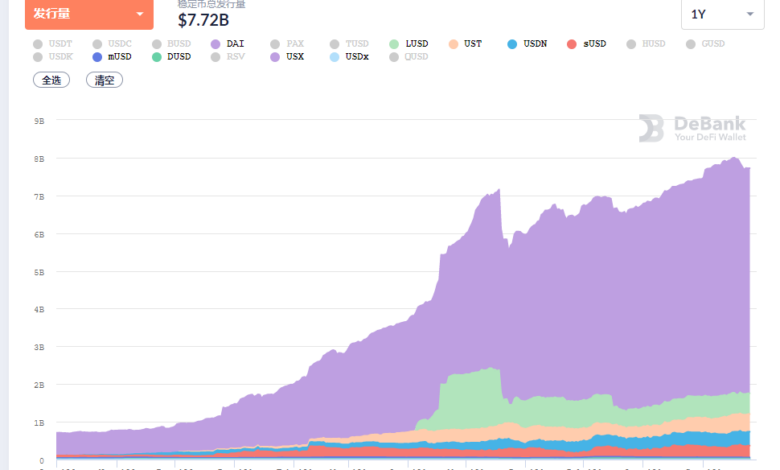
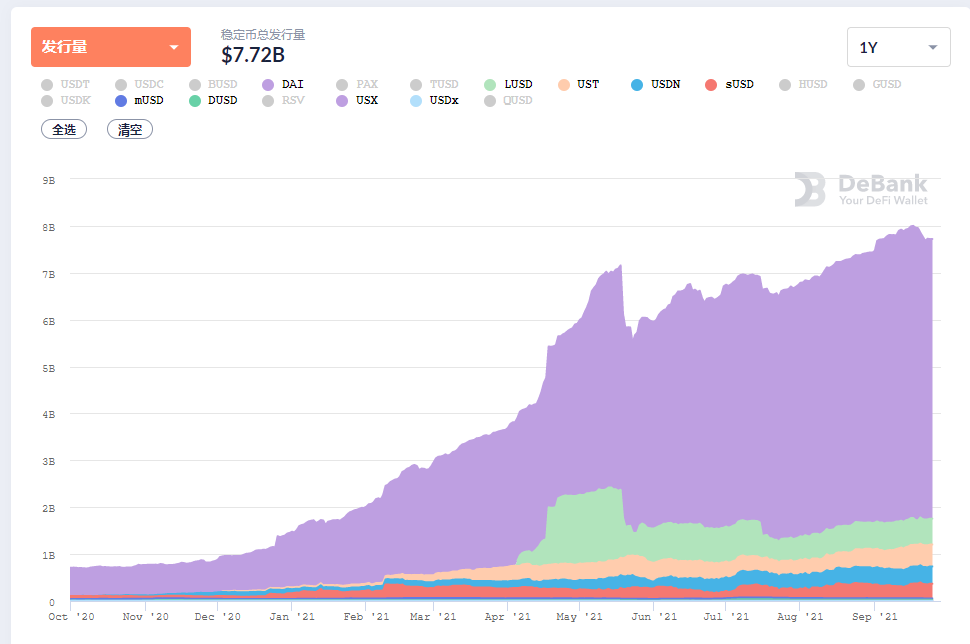
Market Trends
The report identifies significant growth in stablecoin adoption across various DeFi applications. The increased usage of stablecoins for trading, lending, and borrowing within DeFi platforms is a noteworthy trend. The report also notes the rising innovation in stablecoin protocols, with new models emerging that aim to enhance stability and security. Examples include the development of algorithmic stablecoins and decentralized stablecoin protocols.
This suggests a trend towards greater diversity and competition within the stablecoin market.
The DeFi Htx Ventures report highlighted the crucial role of stablecoins and RWA’s in the burgeoning DeFi space. Interestingly, as US stocks navigated a potential market meltdown, the bitcoin price retook the $80k mark ( bitcoin price retakes 80 k as us stocks avoid black monday meltdown ), suggesting a resilience in the cryptocurrency market. This stability, despite broader market anxieties, further underscores the potential of stablecoins and RWA’s in providing a degree of security within the DeFi ecosystem.
Challenges
Several challenges are presented in the report regarding stablecoins and RWAs. One key challenge is the issue of maintaining the peg to fiat currencies, particularly in the context of volatile market conditions. The report emphasizes the need for robust reserve management and risk mitigation strategies to maintain the peg. Another significant concern is the potential for regulatory scrutiny and the implementation of stringent regulations, which could impact the development and adoption of stablecoins and RWAs.
The report also addresses the challenge of transparency and auditability for reserve assets, highlighting the need for improved mechanisms to ensure the security and reliability of RWAs.
Future Outlook
The report presents a cautiously optimistic outlook for the future of stablecoins and RWAs in DeFi. While acknowledging the existing challenges, it emphasizes the potential for significant growth and innovation in the coming years. The report anticipates that the increasing demand for stablecoins within the DeFi ecosystem will continue to drive innovation and development of new stablecoin protocols. Furthermore, it suggests that advancements in reserve asset management and regulatory compliance could unlock further opportunities for stablecoin and RWA adoption.
The Htx Ventures report highlights the crucial role of stablecoins and rwas in DeFi, but the recent Kips first superior agent trading tournament, showcasing AI-driven market evolution ( kips first superior agent trading tournament concludes showcasing ai driven market evolution ), offers a fascinating glimpse into the future of decentralized finance. Ultimately, the interplay between these stablecoins and rwas, and the increasingly sophisticated AI tools like those demonstrated in the tournament, will likely shape the future of DeFi protocols and their stability.
The report underscores that future success will depend on the ability to address current challenges and adapt to evolving regulatory environments.
Regulatory Implications
The report thoroughly analyzes the implications of regulatory developments on stablecoins and RWAs. It examines the potential impact of regulatory frameworks on the design, implementation, and adoption of these assets. The report emphasizes the importance of regulatory compliance for the long-term sustainability and growth of the stablecoin and RWA markets. The report suggests that the future development of stablecoins and RWAs will heavily depend on the regulatory clarity and approach.
Summary Table of Key Findings
| Category | Key Findings |
|---|---|
| Market Trends | Growing adoption of stablecoins in DeFi, rising innovation in stablecoin protocols, increasing diversity and competition within the stablecoin market. |
| Challenges | Maintaining the peg to fiat currencies, potential for regulatory scrutiny, transparency and auditability of reserve assets. |
| Future Outlook | Optimistic outlook for significant growth and innovation, increasing demand for stablecoins driving innovation, advancements in reserve asset management unlocking further opportunities. |
| Regulatory Implications | Thorough analysis of the impact of regulatory frameworks on stablecoins and RWAs, emphasis on regulatory compliance for long-term sustainability, future development dependent on regulatory clarity and approach. |
Integration and Interoperability: The Role Of Stablecoins And Rwas In Defi Htx Ventures Report
Stablecoins and Real-World Assets (RWAs) are poised to revolutionize DeFi, but their true potential hinges on seamless integration and interoperability across various platforms. This crucial aspect enables users to easily move value between different DeFi applications and services, fostering a more interconnected and dynamic ecosystem. Without robust interoperability, the benefits of these innovative financial instruments are severely limited.The integration of stablecoins and RWAs into DeFi platforms is a complex undertaking, requiring the development of standardized protocols and APIs that facilitate smooth transactions and data exchange.
This process also necessitates the creation of secure and reliable mechanisms to manage and reconcile transactions across different platforms. This is a critical step towards realizing the full potential of these assets in the DeFi space.
Integration of Stablecoins and RWAs in DeFi Platforms
Different DeFi platforms utilize various methods to integrate stablecoins and RWAs. Some platforms employ smart contracts to facilitate tokenized asset transfers and lending. Others use decentralized exchanges (DEXs) to enable trading of these assets. The specific methods vary depending on the platform’s architecture and the nature of the assets being integrated. These methods ensure efficient and secure transactions within the platform’s ecosystem.
The DeFi Htx Ventures report highlights the crucial role of stablecoins and rWAS in the sector, but recent events like the Bybit hack raise serious questions about the security of these systems. A recent post-mortem analysis of the incident, including safe wallet releases, can be found here: safe wallet releases bybit hack post mortem. Ultimately, the report’s conclusions on the role of stablecoins and rWAS in DeFi will need to take these vulnerabilities into account.
Challenges in Achieving Interoperability
Several obstacles hinder the achievement of full interoperability between stablecoin and RWA systems. A key challenge is the lack of standardized protocols and data formats for asset representation. Different platforms may employ incompatible technologies, making it difficult to exchange assets seamlessly. Furthermore, security concerns arise when transferring assets between platforms with varying levels of security. Maintaining trust and security is a crucial factor for enabling interoperability.
Examples of Stablecoins and RWAs Across DeFi Applications
Stablecoins are frequently used in DeFi lending and borrowing protocols, acting as collateral or backing for loans. For instance, USDC is often used in lending protocols, providing a stable and predictable value for borrowers and lenders. RWAs, such as tokenized real estate or commodities, can be used as collateral in decentralized lending platforms, diversifying investment opportunities. This demonstrates the practical applications of stablecoins and RWAs in DeFi.
Role of Standards and Protocols in Enabling Interoperability
Standardized protocols and data formats are essential for facilitating interoperability. The development and adoption of common standards will enable different platforms to understand and exchange assets seamlessly. This includes the development of interoperable smart contracts and the standardization of token representations. These efforts contribute to a more efficient and accessible DeFi ecosystem.
Protocols Facilitating Exchange and Use of Stablecoins and RWAs
Several protocols are facilitating the exchange and use of stablecoins and RWAs. These protocols often utilize decentralized exchanges (DEXs) to enable trading and liquidity provision. For example, decentralized finance (DeFi) protocols, such as Compound, Aave, and MakerDAO, are increasingly integrating stablecoins into their platforms. These protocols are instrumental in the growing use of stablecoins and RWAs within DeFi.
Diagram Illustrating Flow of Stablecoins and RWAs
+-----------------+ +-----------------+ +-----------------+ | DeFi Platform 1 |---->| DeFi Platform 2 |---->| DeFi Platform 3 | +-----------------+ +-----------------+ +-----------------+ | Stablecoin A | | Stablecoin A | | Stablecoin A | | RWA B | | RWA B | | RWA B | +-----------------+ +-----------------+ +-----------------+
This diagram illustrates the simplified flow of stablecoins and RWAs between different DeFi platforms.
The arrows represent the transfer of assets, facilitated by interoperable protocols and standardized formats. This flow highlights the potential for a more interconnected and dynamic DeFi ecosystem.
Regulatory Landscape and Stablecoins/RWAs

The burgeoning DeFi sector, with its innovative stablecoins and reserve-backed assets (RWAs), faces a complex regulatory landscape. Navigating this environment is crucial for fostering trust and ensuring the long-term sustainability of these financial instruments. The lack of clear regulatory frameworks in many jurisdictions can create uncertainty and hinder the widespread adoption of stablecoins and RWAs within the DeFi ecosystem.
The current regulatory landscape for stablecoins and RWAs is fragmented and evolving rapidly. Different jurisdictions are taking varying approaches, leading to a patchwork of regulations across the globe. This inconsistency can create challenges for businesses operating across multiple markets, impacting their ability to develop and deploy innovative financial products. The evolving nature of the technology necessitates a careful consideration of how regulatory frameworks can adapt to keep pace with innovation while maintaining financial stability.
Current Regulatory Approaches to Stablecoins
Stablecoins, often designed to maintain a stable value pegged to a fiat currency or other asset, are subject to varying regulatory scrutiny depending on the underlying mechanism and the jurisdiction. Some jurisdictions view them as traditional financial instruments, while others perceive them as digital assets requiring specific regulations. This disparity creates a complex environment for developers and users.
Current Regulatory Approaches to Reserve-Backed Assets (RWAs)
Reserve-backed assets, relying on reserves to maintain their value, face a similar regulatory challenge. The specific regulations depend on the composition of the reserve and the regulatory classification of the underlying assets. Some jurisdictions may classify these as securities or commodities, while others might categorize them as digital assets, depending on the specific details of the reserve structure.
Examples of Existing Regulatory Frameworks
The United States, for instance, has taken a piecemeal approach to regulating stablecoins, with different agencies overseeing various aspects. The Securities and Exchange Commission (SEC) has focused on stablecoins that function as securities, while the Commodity Futures Trading Commission (CFTC) has shown interest in those that are considered commodities. This approach underscores the complexities in defining the nature of these assets.
Similarly, the European Union has regulations that address certain aspects of stablecoins but the specific application to RWAs is still developing. Other jurisdictions like the UK and Singapore have developed frameworks that are more focused on risk mitigation and consumer protection.
Potential Future Regulatory Developments
Future regulatory developments in the DeFi space will likely focus on areas like stablecoin reserve requirements, transparency standards, and consumer protection measures. The development of comprehensive frameworks for RWAs will likely also be a significant focus. These developments will play a critical role in shaping the future of DeFi and establishing a more stable and predictable environment for innovators and users alike.
Increased international cooperation and collaboration on regulatory standards is essential to mitigate risks and facilitate the responsible growth of the DeFi sector.
Comparison of Regulatory Approaches Across Jurisdictions
| Jurisdiction | Approach to Stablecoins | Approach to RWAs |
|---|---|---|
| United States | Piecemeal approach, SEC and CFTC involvement | Depends on reserve composition and underlying asset classification |
| European Union | Regulations addressing certain aspects of stablecoins | Developing frameworks for RWAs |
| United Kingdom | Focus on risk mitigation and consumer protection | Focus on risk mitigation and consumer protection |
| Singapore | Focus on innovation while maintaining financial stability | Focus on innovation while maintaining financial stability |
| Other Jurisdictions | Varied approaches based on specific regulatory frameworks | Varied approaches based on specific regulatory frameworks |
The table above provides a simplified overview of the varied approaches. Further research is necessary to understand the nuances of each jurisdiction’s regulatory landscape.
The Future of Stablecoins and RWAs in DeFi
The decentralized finance (DeFi) landscape is rapidly evolving, and stablecoins and real-world assets (RWAs) are poised to play a crucial role in shaping its future. These digital assets are fundamentally changing how value is stored, exchanged, and utilized within the DeFi ecosystem, opening new possibilities for financial inclusion and innovation. Their continued growth and adoption hinge on the integration of emerging technologies, regulatory clarity, and innovative designs.
The potential for stablecoins and RWAs to revolutionize DeFi is substantial. Stablecoins, pegged to fiat currencies or other stable assets, offer a crucial bridge between traditional finance and DeFi, enabling seamless integration and fostering broader participation. RWAs, representing real-world assets like commodities or securities, bring a new level of liquidity and diversification to DeFi protocols, allowing users to access a wider range of investment opportunities.
This integration has the potential to democratize access to traditional financial markets and create new financial instruments.
Potential for Stablecoins and RWAs to Shape the Future of DeFi
Stablecoins and RWAs are expected to drive significant growth and diversification within the DeFi ecosystem. They offer a way to mitigate risk and improve the stability of DeFi protocols, leading to increased user adoption and trust. Stablecoins, for example, can be used as collateral for lending and borrowing, improving the overall efficiency and resilience of DeFi platforms.
Expected Impact of Emerging Technologies on the Use of Stablecoins and RWAs
Emerging technologies like blockchain scalability solutions, decentralized identity, and enhanced security protocols will significantly impact the use of stablecoins and RWAs. Increased transaction throughput and lower fees will encourage wider adoption, while improved security measures will foster user trust. For example, advancements in zero-knowledge proofs could enhance privacy and security in DeFi protocols utilizing stablecoins. The ability to seamlessly integrate stablecoins with other emerging technologies, like NFTs, will unlock new opportunities.
Key Factors Influencing Future Growth of Stablecoins and RWAs in DeFi
Several key factors will shape the future growth of stablecoins and RWAs in DeFi. Regulatory clarity and support from governments are essential for fostering a stable and trustworthy environment. Furthermore, innovative designs and solutions that address current challenges, such as scalability and security concerns, will be crucial. User adoption and education are also key drivers, as a greater understanding of these assets will lead to increased utilization.
Elaboration on Potential for Innovation in Stablecoin and RWA Design
Innovation in stablecoin and RWA design will be pivotal in their continued growth. The development of new stablecoin algorithms and mechanisms for maintaining peg stability, along with the introduction of more sophisticated RWA tokenization methods, are key areas for innovation. The potential for stablecoins pegged to multiple assets or baskets of assets will offer diversification and reduced risk.
New mechanisms for collateral management in RWA-backed lending protocols can improve efficiency and reduce operational risks.
Timeline Illustrating Predicted Development and Evolution of Stablecoins and RWAs in DeFi
A detailed timeline for the predicted development and evolution of stablecoins and RWAs in the DeFi space is difficult to create with precise dates. However, several phases can be identified:
- Phase 1 (2024-2026): Increased regulatory scrutiny and the emergence of more robust and stablecoin protocols. This phase will see an increase in the adoption of RWAs for lending and borrowing within DeFi, alongside more sophisticated tokenization methods.
- Phase 2 (2027-2029): Integration of stablecoins and RWAs with other emerging technologies like NFTs and decentralized identity solutions. The emphasis will shift towards enhanced security and user experience.
- Phase 3 (2030-2035): Further innovation in stablecoin designs, with a focus on enhanced resilience and efficiency. RWAs will play a crucial role in broadening access to traditional financial markets within the DeFi ecosystem.
This timeline is not definitive, and the actual pace of development may vary depending on factors such as regulatory frameworks, technological advancements, and market adoption. Nevertheless, stablecoins and RWAs are poised to significantly impact the future of DeFi, offering a more inclusive and innovative financial system.
Epilogue
In conclusion, the HTX Ventures report highlights the significant role of stablecoins and RWAs in shaping the future of DeFi. The report underscores the potential for innovation and growth while also acknowledging the inherent risks and challenges. Ultimately, the report paints a nuanced picture of the evolving landscape, urging a careful consideration of both opportunities and threats in the rapidly changing DeFi space.





