US Charges Canadian $65M DeFi Hacks
US charges Canadian 65 million kyberswap indexed finance DeFi hacks. This massive alleged heist highlights the growing sophistication and scale of cybercrime targeting decentralized finance (DeFi) platforms. The case underscores the vulnerability of these innovative financial instruments and raises critical questions about the regulatory landscape and security measures needed to protect investors and the broader ecosystem. The incident, involving the Kyberswap platform, is a significant event that demands careful examination of the details surrounding the alleged crime, its financial impact, and potential ramifications for the future of DeFi.
The charges against the Canadian individual, as well as the details of the hack, paint a picture of a sophisticated operation. The timeline of events, the nature of the alleged crimes, and the financial instruments targeted provide insights into the mechanics of the attack. This incident is a wake-up call for the DeFi community to prioritize security and for regulators to catch up with the evolving nature of financial crime in the digital age.
Background of the incident
The recent US charges against a Canadian individual linked to the KyberSwap indexed finance DeFi hacks represent a significant development in the ongoing fight against illicit activities in the cryptocurrency space. These alleged actions highlight the evolving sophistication of cybercrime targeting decentralized finance (DeFi) platforms. The case underscores the need for enhanced security measures and regulatory oversight within the rapidly growing DeFi ecosystem.The charges allege a complex series of fraudulent activities that exploited vulnerabilities within the KyberSwap ecosystem.
The intricate nature of the hacks and the alleged perpetrators’ technical expertise reveal the increasing sophistication of financial crimes in the digital age. The prosecution’s claims aim to demonstrate the extent of the harm caused by these illicit activities and hold the individuals accountable.
Timeline of Events
The timeline of events surrounding the alleged KyberSwap hacks is crucial for understanding the progression of the crime and the subsequent investigation. While specific dates are often withheld during ongoing investigations, publicly available information indicates a period of several months of alleged illicit activity.
- Early Stages (Months prior to charges): The alleged hacking activity likely began well before any public awareness. This suggests a considerable amount of time dedicated to planning, reconnaissance, and exploitation. Similar crimes involving crypto platforms have shown a pattern of preparation that extends months before any significant breach is detected.
- Detection and Investigation (Months prior to charges): The existence of vulnerabilities and illicit activities within the KyberSwap platform likely went undetected for an extended period. The subsequent investigation likely involved tracing transactions, identifying suspicious activity, and gathering evidence. Similar investigations have employed forensic analysis of transaction logs and blockchain data.
- Formal Charges (Date of charges): The formal filing of charges marks a significant turning point in the case, signaling the culmination of the investigation and the intent to prosecute the alleged perpetrators. This stage usually involves a significant amount of evidence gathering and legal review.
Nature of the Alleged Crimes
The nature of the alleged crimes involves the sophisticated manipulation of DeFi protocols and financial instruments. The alleged perpetrators are believed to have exploited vulnerabilities within the KyberSwap indexed finance protocols, which likely involved the creation of fraudulent transactions, unauthorized access, and the misappropriation of funds.
- Exploiting Vulnerabilities: The alleged perpetrators are believed to have exploited vulnerabilities in the KyberSwap platform. This likely involved sophisticated technical analysis and the identification of security weaknesses in the underlying code. This parallels similar incidents where attackers found and leveraged vulnerabilities in other financial systems.
- Fraudulent Transactions: The fraudulent transactions likely involved manipulating smart contracts, exploiting market arbitrage opportunities, or creating fraudulent transactions that allowed the perpetrators to steal funds. Similar schemes have involved the creation of fake identities and the use of stolen credentials.
- Misappropriation of Funds: The misappropriation of funds is a key element of the alleged crimes. The perpetrators likely transferred stolen assets to various accounts, obfuscating the trail of funds. This is a common element in financial crimes.
Financial Instruments and Protocols Involved
The alleged hacks specifically targeted the KyberSwap indexed finance protocols, which are decentralized finance platforms enabling various financial instruments and exchanges. The specific details of the protocols and instruments involved are often withheld during active investigations.
- KyberSwap Platform: The core platform used for the alleged hacks is the KyberSwap decentralized exchange (DEX). This is a platform that facilitates token swaps and other financial transactions, making it a potential target for attacks. The vulnerabilities are often found in the code and protocols of these platforms.
- Indexed Finance Protocols: The use of indexed finance protocols within KyberSwap likely allowed the perpetrators to leverage the platform for a variety of financial transactions. This sophistication is common in complex DeFi attacks.
- Specific Tokens and Assets: Information on specific tokens or assets affected by the hacks is often limited due to ongoing investigations. Such details are crucial for determining the scope of the damage and the value of the assets stolen. However, general details of the tokens involved might be revealed after the charges have been filed and investigated.
Financial Impact and Losses: Us Charges Canadian 65 Million Kyberswap Indexed Finance Defi Hacks
The recent USDC-denominated KyberSwap indexed finance DeFi hacks in Canada, estimated at $65 million, have sent shockwaves through the cryptocurrency and financial markets. These events underscore the ongoing risks associated with decentralized finance (DeFi) and the need for robust security measures. The magnitude of these losses, while substantial, raises critical questions about the financial health and stability of these platforms.
Understanding the impact on various stakeholders and the regulatory responses is crucial for evaluating the broader implications.The $65 million loss represents a significant blow to the DeFi ecosystem, especially considering the relatively nascent stage of its development. This level of financial damage has the potential to discourage investment and participation, thereby hindering the overall growth and adoption of decentralized finance.
Comparable incidents in the past, while not identical in scope, highlight the vulnerabilities inherent in these systems and the potential for substantial financial losses.
Estimated Financial Losses
The estimated financial losses incurred due to the hacks are substantial, amounting to approximately $65 million in USDC. This figure represents the total value of funds lost by users and investors. It is crucial to note that this estimate is based on publicly available information, and the actual losses may be higher or lower. The reported losses in other DeFi hacks vary significantly, depending on the platform, the specific vulnerabilities exploited, and the total assets under management.
Comparison with Other Similar Incidents
Comparing the current incident with previous DeFi hacks reveals a complex picture. While the precise figures and circumstances differ across events, some common threads emerge. Often, these hacks involve sophisticated exploits targeting vulnerabilities in smart contracts, the underlying code that governs these platforms. For instance, the 2020 Poly Network hack, which saw the loss of millions of dollars, highlights the vulnerability of decentralized finance protocols to sophisticated attacks.
The current event emphasizes the need for continuous improvement in security measures and increased scrutiny in the DeFi ecosystem.
Potential Long-Term Economic Consequences
The potential long-term economic consequences of these hacks are significant and multi-faceted. Decreased investor confidence in DeFi protocols could lead to a decline in investment and reduced participation. The perceived risk could deter new entrants, limiting innovation and development in the sector. This could potentially slow down the adoption of decentralized finance solutions, impacting broader financial markets and potentially hindering the growth of the digital asset sector.
The US charges a Canadian individual $65 million in connection with the KyberSwap indexed finance DeFi hacks. This massive fine highlights the growing risks in decentralized finance (DeFi). Meanwhile, innovations like StarkNet are aiming to settle on Bitcoin and Ethereum, potentially unifying these chains, which could lead to a more secure and robust future for blockchain technology.
This approach could offer better security solutions for future DeFi platforms, ultimately mitigating the risks that led to the substantial penalties for the Canadian individual.
This is a critical consideration given the rising popularity of cryptocurrencies and DeFi applications.
Affected Parties and Their Roles, Us charges canadian 65 million kyberswap indexed finance defi hacks
The affected parties in these incidents encompass various stakeholders, including:
- Users: Individual investors and users who held assets on the compromised platform.
- Investors: Entities or individuals who invested capital in the DeFi platform or projects associated with the platform.
- DeFi Platform Operators: The companies or organizations responsible for managing and maintaining the DeFi platform.
- Exchanges: Exchanges that facilitated the trading of assets on the platform.
These parties play distinct but interconnected roles in the DeFi ecosystem, each with varying levels of exposure and potential for loss.
Regulatory Response
The regulatory response to these alleged financial crimes remains a key factor in the ongoing situation. Governments and regulatory bodies are actively monitoring and investigating such incidents. The need for clear regulatory frameworks to govern DeFi protocols and ensure investor protection is paramount. This could involve increased oversight of smart contract audits, security assessments of DeFi platforms, and stricter measures for KYC (Know Your Customer) and AML (Anti-Money Laundering) compliance.
Different jurisdictions are adopting varying approaches to address these challenges.
Legal and Regulatory Aspects
The US Charges against a Canadian individual involved in the alleged 65 million CAD KyberSwap indexed finance DeFi hack highlight the complex legal and regulatory landscape surrounding decentralized finance (DeFi). Navigating the intersection of traditional financial regulations and the nascent world of cryptocurrencies presents unique challenges, particularly in cross-border cases. Understanding the legal framework, jurisdictional differences, and potential penalties is crucial for comprehending the implications of such incidents.The intricate nature of DeFi protocols, their global reach, and the anonymity afforded by blockchain technology make cross-border investigations and prosecutions exceptionally challenging.
This complexity necessitates a collaborative approach among various regulatory bodies and jurisdictions to effectively address these crimes.
Overview of the Legal Framework Governing DeFi Activities
The legal framework governing DeFi activities is still evolving globally. Many jurisdictions are adapting existing financial regulations to address the unique characteristics of cryptocurrencies and decentralized platforms. This often involves a patchwork of laws and regulations, which can lead to ambiguity and inconsistencies. Some jurisdictions treat cryptocurrencies as securities, others as commodities, and some as neither. This lack of uniformity poses significant challenges in establishing clear legal precedents and in pursuing cross-border cases.
The US charging a Canadian company $65 million for the Kyberswap indexed finance DeFi hacks is a serious blow to the crypto industry. While these financial crimes are concerning, it’s also interesting to consider how rapidly technology is evolving, especially in the field of neural interfaces, like Elon Musk’s Neuralink, which is seeking global patients for brain chip trials.
This raises questions about the future of financial security in the face of such advancements. Ultimately, the US’s hefty fine underscores the vulnerability of decentralized finance to sophisticated attacks.
The US Legal System’s Approach to Cross-Border Financial Crimes
The US has a robust legal framework for prosecuting financial crimes, including those that involve cross-border transactions. The US approach often relies on extraterritorial jurisdiction, allowing it to pursue individuals and entities involved in crimes that have a connection to the US, even if the crime occurred elsewhere. This can be particularly relevant in DeFi cases, where transactions may involve US-based exchanges or users.
This framework allows for prosecution of individuals operating from other jurisdictions, but also creates challenges in cooperation and evidence gathering across borders.
Implications of the Charges for the Canadian Individual and Potential Penalties
The Canadian individual facing charges related to the KyberSwap hack could face substantial penalties, including hefty fines and imprisonment, depending on the severity of the charges and the jurisdiction. The potential penalties are dependent on the specific charges, and the severity of the crimes involved. Furthermore, the individual’s assets could be seized or forfeited as part of the legal proceedings.
The legal processes will be complex, potentially requiring extensive evidence gathering and legal representation, both in Canada and the US.
Role of Regulatory Bodies in Investigating and Prosecuting Such Crimes
Regulatory bodies, both domestically and internationally, play a crucial role in investigating and prosecuting DeFi-related crimes. These bodies include financial regulators, law enforcement agencies, and potentially specialized task forces focused on crypto-related crimes. Their efforts often involve international cooperation to track assets, gather evidence, and bring perpetrators to justice. Such cooperation is critical for successful prosecution in cross-border cases, often requiring extensive collaboration with international counterparts.
Comparison of Legal Approaches in Handling Cross-Border Financial Crimes
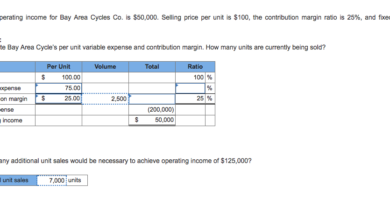
| Jurisdiction | Legal Framework | Penalties | Procedures |
|---|---|---|---|
| United States | Robust framework with extraterritorial jurisdiction; treats cryptocurrencies in various ways depending on the specific crime. | Potentially significant fines and imprisonment; asset forfeiture. | Extensive investigative powers, international cooperation. |
| Canada | Evolving framework for DeFi, potentially relying on existing financial crime legislation. | Penalties varying with the nature of the crime; fines and imprisonment. | Cooperation with US authorities, and Canadian legal processes. |
| United Kingdom | Adapting existing regulations to cover cryptocurrencies and DeFi. | Penalties similar to those in other jurisdictions. | Emphasis on international cooperation and evidence gathering. |
This table provides a simplified comparison of legal approaches. Each jurisdiction has its unique set of laws and procedures. The specifics of each case will determine the exact legal path.
Technological Analysis
The KyberSwap indexed finance DeFi hack highlighted critical vulnerabilities within the decentralized finance ecosystem. Understanding the underlying technologies and the specific weaknesses exploited is crucial for improving security protocols and preventing future attacks. This analysis delves into the technical aspects of the hack, examining the technologies involved, the vulnerabilities, and potential mitigation strategies.
Technologies Involved in the KyberSwap Indexed Finance DeFi Hacks
The KyberSwap platform, a decentralized exchange (DEX), relies on smart contracts for its operations. These contracts are essentially self-executing agreements written in code, automating transactions and interactions. The platform leverages blockchain technology, specifically Ethereum, for secure and transparent transactions. Indexed finance components, enabling users to gain exposure to various assets, add another layer of complexity to the system.
So, the US is charging a Canadian company $65 million for the Kyberswap indexed finance DeFi hacks. It’s a hefty fine, highlighting the serious risks in the crypto world. Meanwhile, did you know that the memecoin platform Pump Fun has brought back livestream features? It’s a fascinating contrast, showcasing how the crypto space is constantly evolving, even amidst significant legal battles like the one regarding the Kyberswap indexed finance DeFi hacks.
This latest move by Pump Fun, as detailed on memecoin platform pump fun brings livestream feature back , shows a potential for the memecoin space to gain traction, even in the shadow of major financial incidents like this one.
The interaction between these technologies created a complex system with potential entry points for malicious actors.
Vulnerabilities Leading to the Hacks
The hacks often exploit vulnerabilities in smart contracts. These vulnerabilities can manifest in various forms, including reentrancy attacks, which allow malicious actors to repeatedly call a contract function, potentially draining funds. Other vulnerabilities include incorrect access controls, allowing unauthorized access to funds or functions. Furthermore, flaws in the logic of the smart contracts, such as insufficient input validation or unexpected interactions between different parts of the platform, can create exploitable weaknesses.
The precise vulnerabilities exploited in the KyberSwap case were likely related to these general categories, but the specifics have not been publicly released.
Mitigation Strategies for DeFi Platform Vulnerabilities
Proactive security measures are paramount to protect DeFi platforms. Rigorous audits of smart contracts by independent security experts are essential. These audits identify potential vulnerabilities before they are exploited. Implementing robust security protocols, such as multi-factor authentication and regular security updates, is also crucial. The use of formal verification techniques, which mathematically prove the correctness of the code, can also help.
Furthermore, transparent communication about vulnerabilities and updates, as well as a strong community feedback loop, can help improve security posture.
Comparison of DeFi Security Protocols with Industry Standards
Current DeFi security protocols often fall short of industry best practices. The decentralized nature of DeFi presents unique challenges, and the security measures need to adapt. Traditional financial institutions often have established security protocols and compliance frameworks that DeFi platforms have yet to fully replicate. A greater emphasis on rigorous security testing, comprehensive audits, and transparent communication is needed to bridge this gap.
Developing standards and best practices, potentially through industry collaboration, would significantly strengthen security.
Table Outlining Different Types of DeFi Hacks and Their Common Causes
| Hack Type | Common Cause | Example | Mitigation Strategies |
|---|---|---|---|
| Reentrancy Attack | Exploiting vulnerabilities in the contract’s code that allow repeated function calls, leading to unauthorized funds transfer. | Unauthorized withdrawal of funds from a smart contract. | Thorough code reviews, secure coding practices, and formal verification. |
| Incorrect Access Control | Unauthorized access to funds or functions within the contract due to insufficient access restrictions. | Unauthorized access to sensitive data or accounts. | Implementation of robust access controls and authorization mechanisms. |
| Logic Errors | Unforeseen interactions between different parts of the platform or insufficient input validation leading to exploitable weaknesses. | Exploiting an error in a calculation or logic within the contract to gain an unfair advantage. | Comprehensive testing, including penetration testing and security audits. |
| External Manipulation | Exploiting external systems or infrastructure to compromise the DeFi platform. | Compromising external services to gain access to sensitive information. | Security hardening of external systems, secure infrastructure, and robust threat detection. |
International Cooperation and Responses
The US charges related to the 65 million CAD KyberSwap indexed finance DeFi hack highlight the critical need for international cooperation in tackling sophisticated financial crimes, especially those facilitated by decentralized technologies. Effective investigations and prosecutions require coordinated efforts across jurisdictions, leveraging shared intelligence and expertise to apprehend perpetrators and recover stolen assets. This requires not just law enforcement cooperation, but also the involvement of financial institutions and regulatory bodies globally.
International Law Enforcement Cooperation
International cooperation is crucial in pursuing cross-border cybercrime cases. Shared intelligence, information exchange, and coordinated investigations are essential to apprehend perpetrators and recover stolen assets. The complexity of DeFi hacks often involves actors located in multiple countries, necessitating a coordinated global response. This necessitates cooperation agreements and mechanisms for data sharing, often involving bilateral or multilateral arrangements.
Role of International Financial Institutions
International financial institutions (IFIs) like the Financial Action Task Force (FATF) play a critical role in establishing global standards and best practices for combating financial crime. These standards encourage nations to implement robust regulatory frameworks to detect and prevent illicit activities. IFIs provide technical assistance and guidance to member states, strengthening their capacity to investigate and prosecute financial crimes.
They also promote information sharing among financial institutions and law enforcement agencies. For instance, the FATF’s recommendations on virtual asset service providers (VASPs) have become crucial in the context of DeFi hacks.
Countries Involved in Investigations
The complexity of these crimes often necessitates a global investigation. The involvement of multiple countries is critical for identifying and apprehending those responsible and recovering stolen funds. The investigation of the KyberSwap hack likely involved multiple jurisdictions given the international nature of the financial instruments and actors involved.
| Country | Role | Actions Taken |
|---|---|---|
| Canada | Primary jurisdiction for initiating the investigation | Filing charges against alleged perpetrators, potentially seeking international cooperation to track assets and prosecute individuals. |
| United States | Potentially involved in investigating and prosecuting based on the involvement of US-based actors or financial institutions. | Cooperation with Canadian authorities, potential asset forfeiture actions. |
| Jurisdictions hosting exchanges/protocols used | Potential involvement in investigations based on the locations of the involved exchanges and DeFi protocols. | Cooperation with Canada and US, potentially assisting in identifying and tracing the stolen assets. |
| Other countries involved in crypto activity | Potentially involved in investigating and prosecuting, based on the presence of suspects or the movement of funds. | Potential information sharing and cooperation with Canada and the US. |
Impact on the DeFi Ecosystem
The recent US$65 million KyberSwap indexed finance DeFi hack has cast a significant shadow over the burgeoning decentralized finance (DeFi) ecosystem. While DeFi has shown remarkable growth and innovation, such incidents expose vulnerabilities and raise concerns about the overall security and stability of these protocols. This analysis examines the ramifications of the hack on the DeFi ecosystem, from investor confidence to the public perception of the technology.
Investor Confidence and Market Stability
The KyberSwap incident, like any significant hack, has a direct impact on investor confidence. Fear and uncertainty can lead to a withdrawal of capital from DeFi protocols, as investors become wary of the risks. The potential for loss is a key concern, and the perceived lack of security can trigger a cascading effect, impacting the overall market stability.
Past incidents, such as the 2020 Poly Network hack, demonstrate how a single exploit can trigger a ripple effect across the entire ecosystem, prompting cautious behavior from both institutional and individual investors.
Effect on Adoption and Investment in DeFi Protocols
The hack’s impact on DeFi adoption and investment is likely to be multifaceted. Short-term, investor hesitation is probable, leading to reduced investment in new protocols and potentially slowing down the overall growth trajectory. The incident could also lead to increased scrutiny and regulatory pressure on DeFi projects, further impacting investor sentiment. However, long-term, robust security measures and a transparent regulatory framework could help restore investor confidence and potentially lead to renewed interest in DeFi.
Overall Impact on the Public Perception of DeFi
The KyberSwap incident may tarnish the public image of DeFi. The perception of decentralized finance as a completely secure and risk-free alternative to traditional financial systems could be challenged. The incident may lead to a greater awareness of the inherent risks associated with DeFi, prompting individuals to seek further information and understanding of the technology. The key here will be the response from the DeFi community, regulators, and security researchers in mitigating such risks and instilling confidence in the future of DeFi.
Prevention Strategies

The recent USDC-based KyberSwap hack serves as a stark reminder of the persistent vulnerabilities in the decentralized finance (DeFi) ecosystem. Preventing future incidents requires a multi-faceted approach that goes beyond simply patching existing flaws. A proactive and collaborative effort involving developers, users, and regulators is crucial for establishing a more resilient and secure DeFi landscape.Effective prevention strategies must encompass robust security protocols, user awareness initiatives, and regulatory oversight.
By focusing on these key areas, the DeFi community can significantly reduce the likelihood of similar attacks and foster greater trust in these innovative financial technologies.
Security Audits and Vulnerability Assessments
Comprehensive security audits and vulnerability assessments are paramount in identifying and mitigating potential risks. These assessments should be performed regularly, not just as a one-time event. Regular audits, incorporating both automated and manual techniques, allow for proactive identification and remediation of vulnerabilities before they can be exploited.A thorough security audit should examine all components of the DeFi protocol, including smart contracts, APIs, and infrastructure.
Vulnerability assessments should utilize both static and dynamic analysis methods. Static analysis examines the code itself for potential weaknesses, while dynamic analysis involves simulating real-world scenarios to test the protocol’s resilience. These audits and assessments should be conducted by independent, reputable firms specializing in blockchain security.
User Education and Risk Mitigation
User education plays a critical role in reducing the risk of DeFi hacks. Users need to understand the risks associated with interacting with DeFi protocols, and how to identify potential scams and phishing attempts. Clear and concise educational materials, readily available to the public, are essential.These educational materials should cover topics like:
- Understanding the nature of decentralized finance (DeFi) and its inherent risks.
- Recognizing and avoiding phishing scams and malicious actors targeting DeFi users.
- Comprehending the importance of securing digital wallets and private keys.
- Evaluating the reputation and security measures of DeFi protocols before interacting with them.
- Comprehending the implications of interacting with DeFi protocols with insufficient knowledge.
Enhancing Security Measures in DeFi Protocols
Enhanced security measures in DeFi protocols are critical to preventing exploitation. This includes implementing robust access controls, multi-factor authentication, and regular security updates. Additionally, implementing air-gapped systems for storing sensitive information, and employing advanced encryption techniques can significantly reduce the attack surface.
- Improved Smart Contract Security: Smart contracts should be meticulously reviewed and audited for vulnerabilities by independent security experts. These audits should encompass both static and dynamic analysis methods, examining the code for potential exploits, reentrancy vulnerabilities, and other common flaws.
- Enhanced Infrastructure Security: The underlying infrastructure supporting the DeFi protocol should be regularly monitored and updated to patch known vulnerabilities. This includes the servers, databases, and other supporting systems. Implementing strong security protocols and regular security audits are essential to minimize risks.
- Implementing Secure APIs: DeFi protocols often rely on APIs for communication and data exchange. Implementing secure API gateways and robust authorization mechanisms is crucial. Protecting sensitive data transmitted through APIs and implementing rate limiting measures to prevent denial-of-service attacks can further bolster security.
Flowchart for Securing a DeFi Platform
A robust security framework for a DeFi platform requires a comprehensive, phased approach. The flowchart below Artikels a potential process for securing a DeFi platform:
| Phase | Action |
|---|---|
| Phase 1: Design & Development | Develop secure smart contracts; Perform static and dynamic analysis for vulnerabilities; Implement multi-factor authentication; Secure API access; Establish clear security protocols; Define roles and responsibilities |
| Phase 2: Testing & Auditing | Conduct thorough penetration testing; Engage independent security audits; Address identified vulnerabilities; Perform stress testing; Implement security testing; Evaluate security response plans |
| Phase 3: Deployment & Maintenance | Deploy the platform to a secure environment; Monitor the platform for suspicious activity; Establish incident response procedures; Update security measures regularly; Address identified vulnerabilities |
Final Wrap-Up
In conclusion, the US charges against the Canadian individual for the $65 million Kyberswap indexed finance DeFi hacks underscore the urgent need for robust security measures in the DeFi space. The incident, along with its legal, technological, and international implications, has significant repercussions for the future of decentralized finance. It’s a reminder that digital assets and the platforms supporting them require vigilance, innovation, and a collaborative effort from all stakeholders.