Ex-PM X Account Hack Sham Coin Promotion
Former malaysian prime minister x account hacked promote sham coin – Former Malaysian Prime Minister X’s account hacked to promote a sham coin. This incident highlights the vulnerability of high-profile figures to cyberattacks, and the devastating impact such schemes can have. Criminals likely exploited sophisticated social engineering tactics to gain access to the account, then used it to push a fraudulent cryptocurrency. Understanding the tactics behind these scams is crucial for protecting ourselves from similar schemes.
The scheme likely involved a carefully crafted campaign to promote the sham coin, using social media platforms and potentially other channels. This paragraph will delve into the specific methods of the attack, the characteristics of the sham coin, and the motivations behind the cybercriminals. We’ll also explore the common red flags associated with fraudulent cryptocurrency projects.
Account Compromise and Fraudulent Activities
A recent hacking incident targeting a former Malaysian Prime Minister’s social media account highlights the vulnerability of high-profile figures to sophisticated cyberattacks. The perpetrator(s) exploited the account to promote a fraudulent cryptocurrency scheme, causing significant reputational damage and potentially impacting the public’s trust in online platforms. This incident serves as a stark reminder of the growing sophistication of online fraud and the need for robust security measures.
Account Hacking Incident Summary
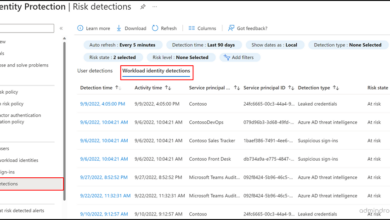
The former Prime Minister’s account was compromised, likely through a combination of social engineering and technical exploits. This involved unauthorized access to the account and the subsequent dissemination of fraudulent content. The attack leveraged the victim’s high profile to increase the perceived legitimacy of the scam.
Methods of Account Compromise
Several methods are commonly employed to compromise high-profile accounts. These include phishing attacks, where victims are tricked into revealing login credentials, or malware infections that exploit vulnerabilities in software. Social engineering tactics, like manipulating individuals into revealing sensitive information, are also frequently used. Sophisticated password-cracking techniques and exploiting weaknesses in security protocols are also part of the arsenal of attackers.
Motive: Financial Gain
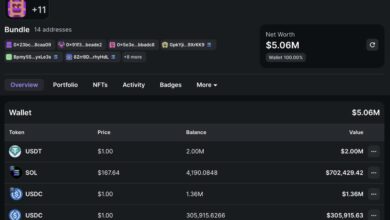
The primary motive behind the hacking was likely financial gain. The fraudulent cryptocurrency promotion aimed to attract investors, who were then tricked into parting with their money in the hope of significant returns. This is a common tactic in cryptocurrency scams, where attackers capitalize on the public’s interest in potentially high-profit investments. Examples of such scams abound, demonstrating the relentless pursuit of financial gain through cybercrime.
Characteristics of a Sham Cryptocurrency Promotion
A sham cryptocurrency promotion typically involves several key characteristics. These include promises of unrealistic returns, the use of misleading information, and the pressure to invest quickly. The promoters often use high-profile figures or individuals to enhance the legitimacy of the scheme. They also tend to use technical jargon and buzzwords to obscure the true nature of the investment.
These characteristics often attract victims looking for quick profits, as the allure of easy wealth is a common vulnerability in investment schemes.
Potential Damage and Risks
The fraudulent cryptocurrency promotion poses significant damage to both the victim and the public. The former Prime Minister’s reputation suffered considerable damage, as their account was used to endorse a clearly fraudulent scheme. The public may also lose confidence in the platform used for the promotion. The potential financial losses for investors are substantial, and the scheme often involves complex transactions, making it challenging for victims to recover their funds.
The risk of financial ruin and reputational damage is high, as the perpetrators often employ sophisticated tactics to obscure their activities.
Common Social Engineering Tactics
| Social Engineering Tactic | Description | Example | Impact ||—|—|—|—|| Phishing | Sending deceptive emails or messages to trick victims into revealing personal information, such as login credentials. | Email claiming to be from a bank asking for account details. | Account compromise, data theft. || Spear Phishing | Targeted phishing attacks directed at specific individuals or organizations, often leveraging detailed knowledge of the victim.
| Email from a company CEO asking for urgent transfer of funds. | Account compromise, data theft, financial loss. || Baiting | Enticing victims with something of value, such as a reward or prize, to trick them into revealing information. | Offer of free software or gift cards in exchange for login details. | Account compromise, data theft.
|| Pretexting | Creating a fabricated scenario to gain trust and extract sensitive information. | Pretending to be a technical support representative to gain access to accounts. | Account compromise, data theft, financial loss. || Quid Pro Quo | Offering something in exchange for information or access. | Offering a job in exchange for login credentials.
| Account compromise, data theft. |
So, this former Malaysian PM’s account getting hacked and promoting a bogus cryptocurrency is pretty shady, right? It’s a classic case of exploiting trust for personal gain. But it also mirrors the current market trends, like how fake tariff news is pumping up the market and making people eager to invest, like in fake tariff news pump shows market ready to ape.
It just highlights how easily people can be manipulated in this volatile environment, which sadly isn’t new, even if the methods used to scam people are evolving. The whole thing is a reminder that verifying information is crucial, especially in the digital age. These hacked accounts are like the latest scams in the crypto space, sadly.
Cryptocurrency Promotion and Scams: Former Malaysian Prime Minister X Account Hacked Promote Sham Coin
The proliferation of cryptocurrency has attracted both legitimate investment opportunities and sophisticated scams. Distinguishing genuine projects from fraudulent ones requires vigilance and a critical eye. This discussion will explore common red flags, compare legitimate and illegitimate projects, examine potential psychological manipulation tactics, detail the stages of a typical scam, and define the characteristics of a sham coin. Understanding these aspects is crucial for safeguarding investments and avoiding financial losses.
Common Red Flags in Fraudulent Cryptocurrency Promotions, Former malaysian prime minister x account hacked promote sham coin
Identifying fraudulent cryptocurrency promotions requires a keen awareness of red flags. These indicators often signal a potential scam. Look for promises of unrealistic returns, a lack of transparency regarding the project’s team and operations, and aggressive marketing tactics. Unverified or anonymous social media accounts associated with the promotion should also raise suspicion. Rapidly increasing prices without substantial backing or credible developments are another red flag.
Claims of government endorsements or partnerships without official documentation should be viewed with extreme caution.
Comparison of Legitimate and Illegitimate Cryptocurrency Projects
| Feature | Legitimate Project | Illegitimate Project |
|---|---|---|
| Team and Background | Transparent and verifiable information about the development team, including their experience and expertise in the relevant fields. Proven track record of successful projects is desirable. | Anonymous or unverified team, lacking experience or expertise. May use misleading or fabricated backgrounds. |
| Project Roadmap and Development | A clear and detailed roadmap outlining the project’s milestones, features, and development timeline. Regular updates and progress reports are provided. | Vague or non-existent roadmap, lack of transparency regarding development progress. Often promises unrealistic timelines. |
| Tokenomics | Detailed tokenomics, explaining the token’s utility, distribution, and potential use cases within a functioning ecosystem. Mechanisms for value creation and community participation are explained. | Unsubstantiated or misleading tokenomics, often designed to inflate value or create a sense of urgency without a clear use case or purpose. |
| Community Engagement | Active and engaged community participation with opportunities for users to contribute to the project’s growth. Authentic interactions with users are encouraged. | Inauthentic or fabricated community engagement, often involving paid shills or bots to create a false sense of popularity. |
Psychological Manipulation Techniques in Cryptocurrency Promotions
Fraudulent promoters frequently utilize psychological manipulation techniques to exploit investor emotions. These techniques include creating a sense of urgency or scarcity, playing on fear of missing out (FOMO), and leveraging the allure of high returns. They often employ emotional appeals and testimonials to persuade investors. The pressure to invest quickly can cloud judgment, leading to hasty decisions.
Furthermore, social proof and influencer marketing are frequently exploited to legitimize the project.
Stages of a Cryptocurrency Scam
A typical cryptocurrency scam involves several distinct stages. The initial stage often involves creating hype and excitement around a new cryptocurrency. This is followed by aggressive marketing, frequently leveraging social media and influencers. The next stage often involves creating a sense of urgency, pressuring potential victims to invest quickly. The scam culminates with the disappearance of funds or the project’s collapse.
This final stage often involves the manipulation of the project’s narrative to cover up the fraudulent activity.
Characteristics of a Sham Coin
A sham coin typically lacks a genuine use case, or its purported use case is exaggerated or non-existent. The team behind the coin may be anonymous or unverified. Rapid price fluctuations without corresponding developments are a common indicator. Aggressive marketing and promotional activity, often involving paid influencers, are prevalent. There is frequently a lack of transparency and disclosure regarding the project’s operations and finances.
Finally, a sudden and unexplained disappearance of the project’s website or social media presence often signals a scam.
Impact on Public Trust and Reputation
The hacking of a former Malaysian Prime Minister’s social media account, coupled with the promotion of a fraudulent cryptocurrency, has far-reaching implications, particularly regarding public trust in political figures, digital security, and financial institutions. This incident underscores the vulnerability of even high-profile individuals to sophisticated cyberattacks and the potential for widespread damage to reputation and public confidence.This incident exposes a critical weakness in online security and highlights the potential for financial harm, not just to the individual but also to the public.
The actions taken by the hackers, aiming to manipulate public opinion and potentially gain financial advantage through a fraudulent cryptocurrency, have significantly impacted the public’s perception of the former Prime Minister and the wider political landscape. The consequences of such actions extend beyond the immediate impact on the individual and potentially damage the public’s faith in online security measures and financial systems.
Just heard that former Malaysian PM X’s account was hacked and used to promote a scam cryptocurrency. This is incredibly concerning, especially considering that a respected analyst believes Bitcoin is on the verge of its largest price drawdown of the bull market, as reported here. It really highlights how vulnerable even high-profile figures can be in the world of digital currencies, and how important it is to be cautious about any investment opportunities presented via social media.
Hopefully, the situation with PM X’s account will be resolved quickly and the victims will be protected.
Public Perception of the Former Prime Minister
The former Prime Minister, prior to the incident, likely enjoyed a degree of public trust and recognition. This trust was likely associated with his political role and public persona. The hacking incident, coupled with the fraudulent promotion, has undoubtedly eroded that trust. This erosion is likely to be felt most strongly among supporters who may now question his integrity and judgment.
Moreover, those who had previously held negative views of the former Prime Minister may use this event to reinforce existing negative perceptions.
Impact on the Political Figure’s Reputation
The hacking incident has undeniably damaged the former Prime Minister’s reputation. The association with a fraudulent cryptocurrency promotion, especially in the context of a high-profile political figure, has created a negative image. This damage is likely to persist, impacting future endeavors, both political and otherwise. The public will likely perceive the former Prime Minister as susceptible to manipulation and potentially naive about online security risks.
Potential Consequences on Public Trust
The incident has the potential to significantly erode public trust in digital security and financial institutions. The ability of hackers to compromise high-profile accounts and promote fraudulent schemes underscores the vulnerability of individuals and institutions alike. This could lead to increased skepticism about the safety of online transactions and investments, impacting individuals’ willingness to engage in online financial activities.
The potential for financial loss is a significant concern for the public.
Cybersecurity Awareness and Protection Measures
The incident underscores the importance of cybersecurity awareness and robust protection measures. It is crucial for individuals and institutions to understand the risks associated with online activity and take proactive steps to safeguard themselves. This includes using strong passwords, enabling multi-factor authentication, and being cautious about suspicious emails, links, and social media posts. The event also highlights the need for enhanced security protocols for public figures, recognizing their heightened vulnerability.
So, this whole thing about former Malaysian PM X’s account getting hacked to promote a fake cryptocurrency is pretty shady. It’s a reminder of the dangers of online scams, especially when high-profile figures are targeted. Meanwhile, the debate around Ethereum rollbacks, as highlighted in this article on the technical complexities of the issue by an Ethereum core developer ethereum rollback debate technically intractable eth core developer , shows how intricate these issues can be.
Ultimately, it all points back to the ongoing problem of scammers exploiting vulnerabilities in digital systems, whether they’re targeting politicians or blockchain users.
Impact on the Public
| Category | Description | Example |
|---|---|---|
| Financial | Potential loss of money due to fraudulent schemes or decreased trust in online financial institutions. | Individuals losing money through cryptocurrency scams promoted on compromised accounts. |
| Emotional | Increased anxiety and skepticism regarding online safety and security. | Individuals feeling less secure about online transactions and investments following the incident. |
| Political | Erosion of trust in political figures and institutions, potentially leading to decreased voter turnout or political polarization. | A decline in support for the former Prime Minister following the hacking incident. |
Regulatory and Legal Implications

The recent hacking of a former Malaysian Prime Minister’s social media account and subsequent promotion of a fraudulent cryptocurrency highlights the serious legal and regulatory challenges posed by such scams. This incident underscores the need for robust legal frameworks and vigilant regulatory bodies to protect public trust and deter future fraudulent activities. Protecting individuals and the financial system from such malicious acts requires a multi-faceted approach involving both legal frameworks and regulatory oversight.The legal ramifications for those involved in such schemes are significant and can range from hefty fines to imprisonment.
The potential for substantial penalties serves as a deterrent to those considering engaging in similar fraudulent activities. The specific penalties will depend on the nature and severity of the offenses, including the extent of financial losses caused, and the specific laws violated.
Potential Legal Ramifications
Individuals and entities involved in the creation, distribution, and promotion of the sham coin face severe legal consequences. These penalties often include criminal charges for fraud, potentially resulting in substantial prison sentences and financial penalties. The penalties will vary depending on the severity of the actions, the amount of money involved, and the specific laws broken. Criminal prosecution under existing laws for fraud and related offences is a key tool in deterring similar activities in the future.
This includes potential violations of securities regulations, particularly if the promoted cryptocurrency is falsely presented as a legitimate investment opportunity.
Role of Regulatory Bodies
Regulatory bodies play a critical role in combating cryptocurrency scams. They are responsible for establishing and enforcing regulations to ensure the integrity and security of the cryptocurrency market. This involves monitoring transactions, investigating suspicious activities, and taking action against fraudulent schemes. Regulatory bodies must remain proactive in identifying and addressing emerging threats, adapting their strategies to the ever-evolving nature of cryptocurrency technology and scams.
Examples include establishing clear guidelines for cryptocurrency exchanges and platforms, ensuring compliance with anti-money laundering (AML) and know-your-customer (KYC) regulations. Furthermore, they can educate the public about the risks associated with cryptocurrency investment.
Challenges Faced by Law Enforcement
Law enforcement agencies face significant challenges in investigating and prosecuting cryptocurrency scams. One major challenge is the anonymity provided by cryptocurrency transactions. The decentralized nature of many cryptocurrencies makes tracing transactions and identifying the perpetrators difficult. Another challenge is the rapidly evolving nature of cryptocurrency technology. Law enforcement needs to stay updated with the latest developments to effectively investigate and prosecute these crimes.
They need advanced technical expertise to decipher complex crypto transactions and digital forensic tools to effectively analyze the blockchain. Furthermore, effective cooperation between international law enforcement agencies is vital to address transnational cryptocurrency scams.
Legal Frameworks in Place
Malaysia has several laws and regulations in place to address issues related to fraudulent activities in the cryptocurrency market. These regulations, while potentially insufficient in their scope, form the basis for enforcement action. The enforcement of these laws can be a challenge due to the ongoing evolution of cryptocurrency technology and the need for updates to existing frameworks.
| Law/Regulation | Description | Applicability |
|---|---|---|
| Securities Commission Malaysia (SC) regulations | Regulations governing the issuance and trading of securities, including potential application to cryptocurrencies if classified as securities. | To all entities involved in the issuance, trading, or offering of securities in Malaysia. |
| Anti-Money Laundering, Anti-Terrorism Financing Act (AMLATFA) | Regulations to prevent money laundering and terrorist financing, which can be applied to cryptocurrency transactions. | Applies to financial institutions and other entities involved in financial transactions, including those dealing with cryptocurrencies. |
| Criminal Code | General criminal laws that may be applied to fraudulent activities, including those related to cryptocurrency scams. | Applies to all individuals and entities involved in criminal activities. |
Preventive Measures and Recommendations

The recent hacking incident involving a former Malaysian Prime Minister’s account underscores the critical need for robust cybersecurity measures. Protecting public figures, and indeed all online users, from such attacks is paramount. This requires a multi-faceted approach encompassing strong individual practices, enhanced technological safeguards, and proactive awareness training. A proactive stance is crucial in mitigating the risks of account compromise and fraudulent activities.Effective preventative measures are not just about reacting to incidents but also about building a culture of cybersecurity vigilance.
This means understanding the threats, recognizing the vulnerabilities, and consistently implementing the necessary safeguards. By adopting these practices, individuals and organizations can significantly reduce their risk of becoming victims of cyberattacks.
Strong Password Policies and Multi-Factor Authentication
Robust password policies are essential to prevent unauthorized access to online accounts. A strong password is one that is complex, unique, and regularly updated. It should incorporate a mix of uppercase and lowercase letters, numbers, and symbols. Avoid using easily guessable information like birthdays, names, or common phrases. The importance of password complexity cannot be overstated.
A sophisticated password structure is a fundamental line of defense. Employing multi-factor authentication (MFA) adds an extra layer of security. MFA requires users to provide more than one form of verification, such as a code from a mobile app or a security key, before accessing their account. This makes it significantly harder for attackers to gain unauthorized access, even if they have compromised a password.
For example, many online banking services now use MFA to protect user accounts from fraudulent activity.
Cybersecurity Awareness Training
Regular cybersecurity awareness training is crucial for all individuals. This training should cover various aspects of online safety, including identifying phishing attempts, recognizing social engineering tactics, and understanding the importance of secure online behavior. A well-rounded approach to awareness training should address different levels of understanding and provide practical exercises to reinforce learning. For instance, simulated phishing emails can be used to identify vulnerabilities in user responses.
Such training is not a one-time event; it should be a continuous process. Regular updates and refresher courses are essential to keep users abreast of the latest threats and best practices.
Account Security Best Practices
These practices Artikel steps individuals can take to safeguard their online accounts.
| Step | Description | Example |
|---|---|---|
| 1 | Create strong, unique passwords for each online account. | A password like “P@$$wOrd123!” is more secure than “password.” |
| 2 | Enable multi-factor authentication (MFA) whenever possible. | Using a security key or authenticator app adds an extra layer of protection. |
| 3 | Regularly update software and operating systems. | Patches often address vulnerabilities that hackers exploit. |
| 4 | Be cautious of suspicious emails or messages. | Never click on links or attachments from unknown senders. |
| 5 | Report any suspicious activity to the relevant authorities or service providers. | If you suspect your account has been compromised, immediately change your password. |
Conclusive Thoughts
The hacking of former Malaysian Prime Minister X’s account to promote a sham coin raises serious concerns about online security and the potential for financial fraud. This incident serves as a stark reminder of the importance of cybersecurity awareness, especially for high-profile individuals. The public’s trust in digital security and financial institutions could be severely impacted. The article concludes by outlining potential preventive measures, highlighting the importance of robust security protocols and public awareness.